Engineering Articles
April 22, 2026
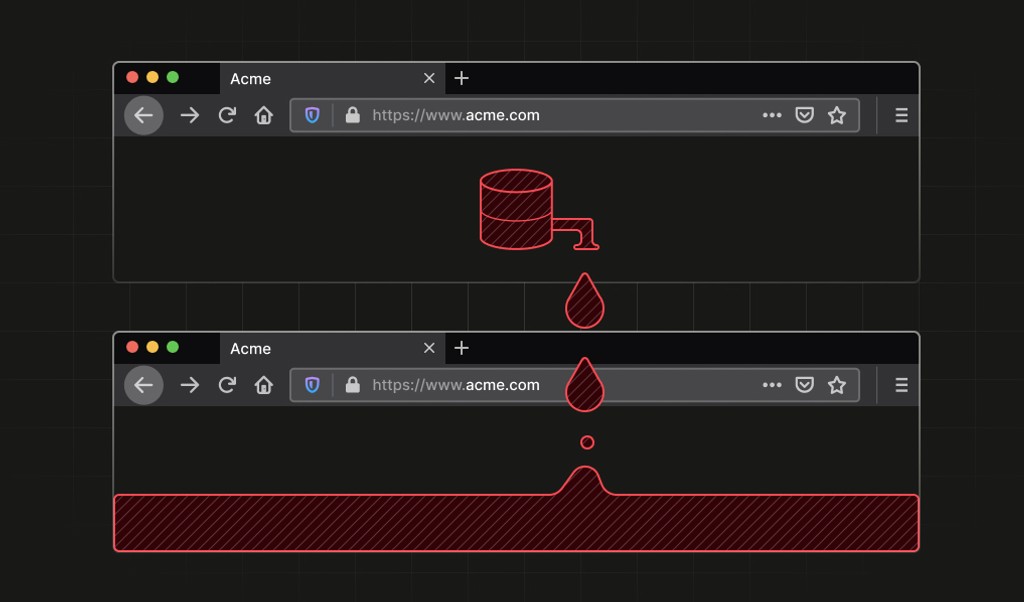
We found a stable Firefox identifier linking all your private Tor identities
We discovered a privacy vulnerability in Firefox Private Browsing and Tor Browser that allows websites to fingerprint and track users across origins using IndexedDB database ordering, even after closing all private windows.
- Fingerprinting
- Engineering