Reveal the true intentions of every visitor — even if they’re anonymous
Make smart, data-driven decisions with Smart Signals to prevent increasingly sophisticated fraud and improve positive experiences for trusted users.
Start Free TrialA single score
trained on your traffic.
Learn MoreImport your fraud data
CSV file
Flag risk without building a model.
Smart Signals are weighted and combined into one score, ready to power your existing risk engine.
Trained on your fraud data.
Upload labeled traffic, Fingerprint trains the model and returns optimized weights.
You stay in control.
Preview the impact on precision and recall before any change goes live. Your team approves update.
Smart Signals
User behavior signals
Incognito Detection
Detect if a user is trying to hide their identity or history.
Browser Tamper Detection
Identify browser spoofing incidents and suspicious browser signature anomalies.
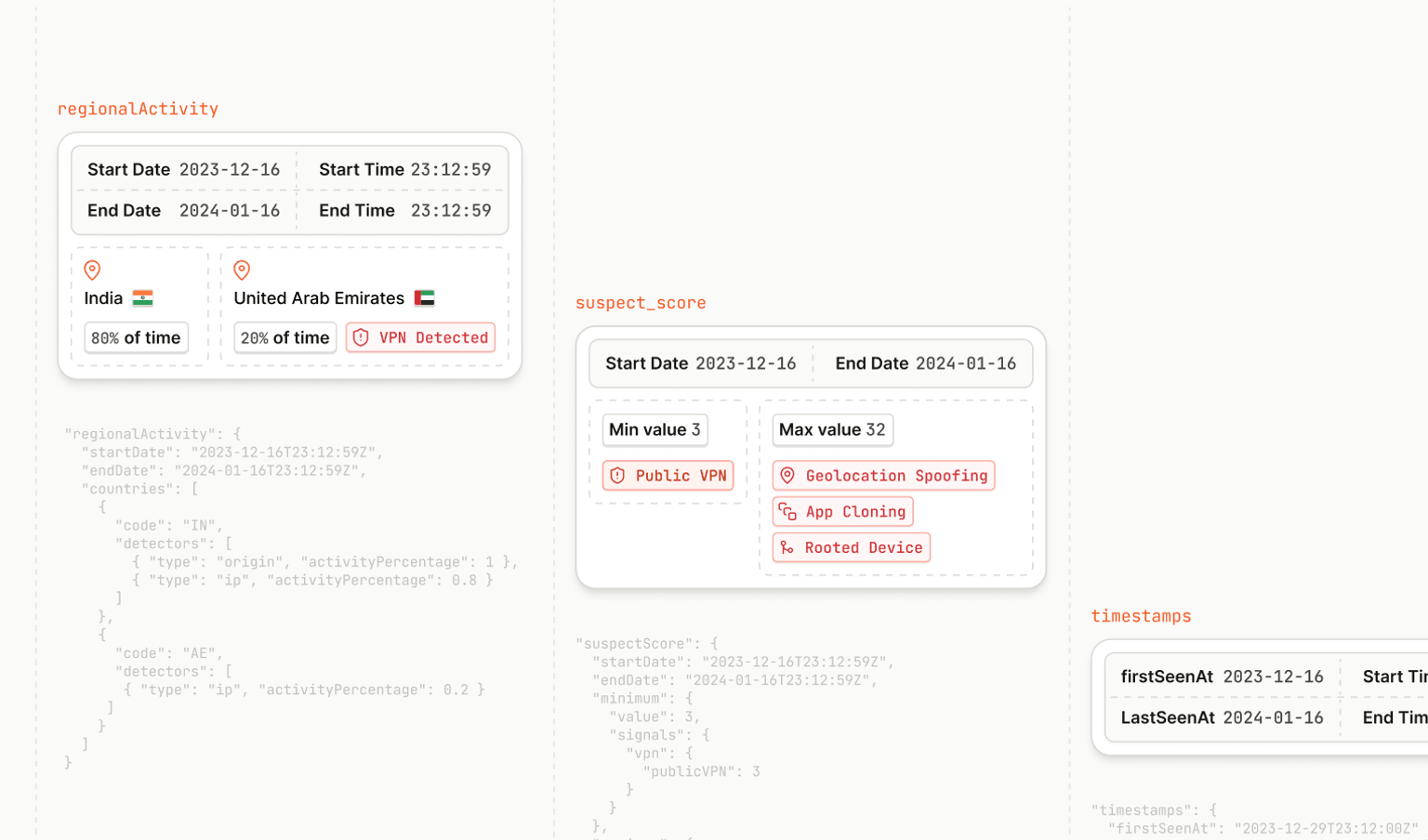
Rooted Device Detection
Ensure a safe Android mobile application environment by detecting rooted devices.
Privacy-Focused Browser
Indicates if a request is initiated from a privacy-focused browser (e.g. Tor) or from a browser whose anti-fingerprinting settings are enabled.
High-activity Device
Flag devices with unusually high activity levels in the past 24 hours.
Velocity Signals
Correlate and identify important data points per visitor at three distinct time-based intervals with Velocity Signals.
Network signals
IP Geolocation
Accurately determine the location of the actual IP address.
VPN Detection
Determine if a user is leveraging a VPN to conceal their identity by validating that their IP time zone matches their browser time zone.
IP Blocklist Matching
See when an IP address matches a known database of malicious actors and spammers.
Bot detection signals
Browser Bot Detection
Identify automated tools, friendly search bots, and other sophisticated threats in real time.
Learn moreAndroid Emulator Detection
Prevent spam and protect against nefarious Android emulator farms by ensuring the request is coming from a physical device.
Virtual Machine Detection
Identify if a request is coming from a virtual machine.
Device data signals
Raw device attributes
Receive an additional set of data including 35 raw browser identification attributes.
Suspect Score
A weighted value of all available Smart Signals, identifying suspicious activity.
Mobile device signals
Cloned App Detection
Identify if a request is coming from a cloned application. (Android only)
Jailbroken Device Detection
Identifies if a visitor is using an iPhone which has been jailbroken. (iOS only)
Frida Detection
Indicates if the open source tool Frida has been used to tamper with the app.
Factory Reset Detection
Indicates the exact time a device was reset to its factory settings, which results in wiping all of the user-sensitive data.
Geolocation Spoofing
Indicates if the user has spoofed the location of their mobile device.
VPN Detection
Determine if a user is leveraging a VPN to conceal their identity on a mobile device.
Man-in-the-Middle Attack Detection
Spots if requests made to Fingerprint were intercepted or altered.
Tampered Request Detection
Detects if critical device properties were changed or faked.
iOS Simulator Detection
Detects when a visitor is using an iOS simulator rather than a real iPhone or iPad. (iOS only)
Pricing
Compare all featuresFree
Web and mobile device identification.
$0
/month
up to 1,000 API calls per month
Includes:
14 day free trial of Pro Plus plan
Fingerprint Identification
Android Smart Signals
500k Android API calls/mo
Free!
Pro Plus
Everything you need starting at
$99
/month for 20K API calls
then $4 per 1,000 additional API calls
Includes:
Fingerprint Identification
Smart Signals
Android Smart Signals
iOS Smart Signals
500k Android API calls/mo
Free!
Enterprise
Build your own plan.
Custom
Customize your plan:
Fingerprint Identification
Access to Additional Smart Signals*
99.9% SLA
Enterprise-grade compliance and security
Proxy integrations
Customer success manager