Summarize this article with
Imagine you get a call from someone claiming to be from your bank. They tell you there's an issue with your account and walk you through installing an app to help resolve it. You go through the process, the bank representative tells you everything is resolved, and the call ends.
A few minutes later, your account is empty.
Unfortunately, that bank rep was fake, and the app you installed was an infostealer capable of collecting your private details, including the one-time passcode (OTP) your bank sends to verify your identity.
This is the anatomy of a growing fraud pattern built around phishing and unregulated Android Package Kit (APK) downloads. Researchers at Cyble documented exactly this playbook targeting customers of a major Indian bank: a fake "complaint tracking" APK distributed via phishing, which granted itself SMS read permissions and silently intercepted OTPs as the fraudster initiated transactions from their own device. No remote control of the victim's phone, no interaction required beyond that first install, just a silent relay that turns a phone into an OTP forwarding machine.
What makes this attack so dangerous is not its technical sophistication but that it defeats the controls banks and other companies put in place to protect their users. The credentials were correct, the OTP was valid, and every check the authentication system was designed to catch passed without issue.
In this post, we'll look at how fraudsters get around these controls using phishing techniques and malware, and how you can detect and prevent them to protect your users.
How the APK attacks work
By the time the fraudster makes that phone call, the hard work is already done. Getting hold of a victim's banking credentials is usually the first step, and there's no shortage of ways to do it. Credentials turn up in data breaches and get sold on dark web marketplaces. Phishing pages that mimic bank login portals trick users into entering their credentials directly. Social engineering campaigns, often delivered over WhatsApp or SMS, create enough urgency that people hand over details without stopping to question why.
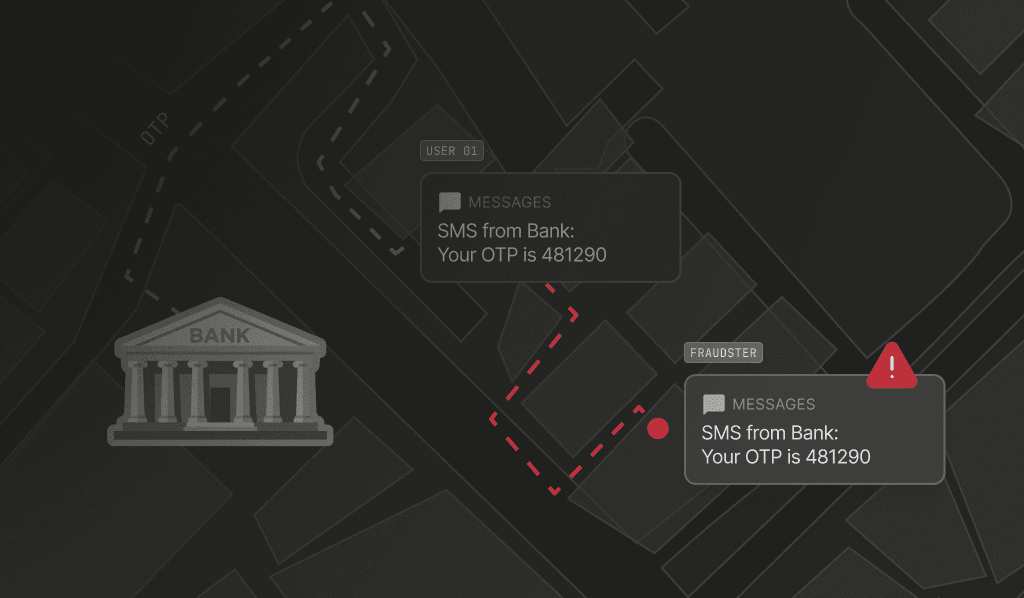
With credentials in hand, the fraudster still has one problem: the OTP. That second factor is the only thing standing between them and the account, and getting around it is where the malicious APK comes in.
Convincing someone to install an unverified app is easier than it sounds, particularly in markets where sideloading, or installing apps from outside official app stores, is common practice. The lure is usually something that feels both legitimate and time-sensitive: a cashback offer, a rewards redemption, a complaint-tracking app, or an account verification tool. The app might be shared via WhatsApp, hosted on a site that looks like the Google Play Store, or sent directly via SMS with a link. Once installed, it asks for SMS read permissions, which sounds harmless enough that most users grant it without a second thought.
After that, the fraudster has everything they need. They open the bank's login page on their own device, enter the victim's stolen credentials, and wait. The bank sends an OTP to the victim's phone, the malicious APK reads it the moment it arrives and silently forwards it to the fraudster in seconds, and they're in. The victim has no idea it happened, and neither does the bank.
The problem with SMS OTP
SMS was designed for reliable message delivery, not secure communication. Its underlying protocol has well-documented vulnerabilities that make messages interceptable in transit, and there's no way for a recipient to verify that a message actually came from the claimed sender. SMS fraud has been a known problem for some time, and it's only growing more prevalent in recent years.
According to Verizon's 2025 Data Breach Investigations Report, 88% of attacks against web applications involve stolen credentials, sometimes as the only action needed, and sometimes as the first step in a larger chain. In the case of phishing APK fraud, it's the latter: credentials get the fraudster to the door, but the OTP is what lets them through it, and an entire criminal ecosystem has emerged to solve exactly that problem.
Zimperium's research team tracked a single SMS stealer campaign running since 2022 that produced over 107,000 unique malware samples, targeted more than 600 global brands, and reached victims across 113 countries, all supported by dedicated development teams, command-and-control servers, and distribution networks built on Telegram bots and fake app store listings.
Awareness campaigns help, but they have limits. The attack described above only requires the victim to install a single app, which means even a cautious user can be caught out by the right lure at the wrong moment.
Why APK attacks are thriving in APAC
Nowhere is this more acute than across the Asia-Pacific region, where a mix of factors has made it a particularly attractive target. Mobile banking adoption and digital payment volumes are high, and SMS OTP is the dominant authentication method across the region. At the same time, sideloading rates are significantly higher than anywhere else in the world.
Here are some alarming stats from Zimperium's 2024 Global Mobile Threat Report that show the scale of the issue:
- 43% of Android devices in APAC sideload apps, the highest rate of any region
- Mobile users who sideload are 200% more likely to have malware running on their devices
- For financial services specifically, 68% of mobile threats were attributed to sideloaded apps
The social engineering lures also work particularly well in developing markets, where fake bonus offers, cashback schemes, and promo redemptions carry more weight.
Across much of the Asia-Pacific region, high mobile payment adoption, price-sensitive users, and a culture of sideloading have created near-ideal conditions for this fraud to thrive.
- India alone accounts for 37% of global smishing attacks, making it the top target country in the world (Zimperium)
- Phishing websites targeting the Philippines jumped 423% from 2024 to 2025 (Check Point Research)
Regulators in the region have taken notice and are working to raise awareness and enforce stronger security practices. Some examples include:
- India: The Reserve Bank of India (RBI) issued Authentication Mechanisms for Digital Payment Transactions Directions, requiring all payment providers to implement stronger two-factor authentication and move beyond sole reliance on SMS OTPs.
- Philippines: The Bangko Sentral ng Pilipinas issued Circular 1213 in May 2025, requiring banks to adopt phishing-resistant authentication methods, such as biometrics or passkeys, and to phase out SMS OTP for high-risk transactions by June 2026.
- Singapore: The Monetary Authority of Singapore (MAS) moved major retail banks off SMS OTP for account logins in 2024.
- Malaysia: Bank Negara Malaysia directed banks to migrate away from SMS OTP and restrict authentication to a single nominated secure device.
The regulatory direction across the region is consistent: SMS OTP alone is no longer acceptable, and stronger device-bound authentication is where things are heading.
How device intelligence helps stop APK attacks
Authentication has traditionally relied on three factors: something you know (such as a password), something you have (such as a physical device), and something you are (such as biometrics). SMS OTP was widely adopted as a practical stand-in for the possession factor, on the assumption that only the account holder would receive the message.
This attack breaks that assumption entirely. The fraudster has the password, and the malicious APK silently delivers the OTP to them as if they were the ones holding the device. Device intelligence doesn't replace those authentication factors, but it adds context that can expose the attack even when other factors appear to pass.
There are a few ways you can layer in device intelligence to help strengthen accounts:
Device binding: Many APAC regulators have already mandated SIM binding for mobile banking apps, addressing a significant portion of this attack vector on mobile. The remaining gap is largely in web banking, where SIM binding doesn't apply and password plus OTP is still the default. By registering a stable device identifier to an account at onboarding, any subsequent login attempt from an unrecognized device triggers step-up authentication or re-KYC. The fraudster can have valid credentials and a correctly entered OTP, but they can't produce a device identifier they've never had access to.
Device consistency checks: Within an active session, a shift in device signals or inconsistencies during a login flow can signal malicious intent. Device context can also catch spoofing attempts and manipulations that introduce subtle inconsistencies as they try to mimic legitimate device environments.
Simultaneous session detection: The login flow should occur on the device that initiated it. Two login attempts for the same account from two distinct devices within a short time window is a strong signal that something coordinated is happening. For example, when a fraudster calls the victim and gets them to open their banking app at the same time they’re logging in.
Bot detection: When a malicious APK intercepts and submits an OTP programmatically rather than a person typing it in, the behavioral signals around that submission, timing, input patterns, and interaction characteristics can indicate automation rather than a human completing the flow.
None of these layers is a complete solution on its own, and device intelligence works best as part of a broader stack that includes stronger authentication methods, fraud monitoring, and a move away from SMS OTP. But as a signal layer, it catches what credential and OTP verification alone cannot.
Strengthening authentication with industry-leading device intelligence
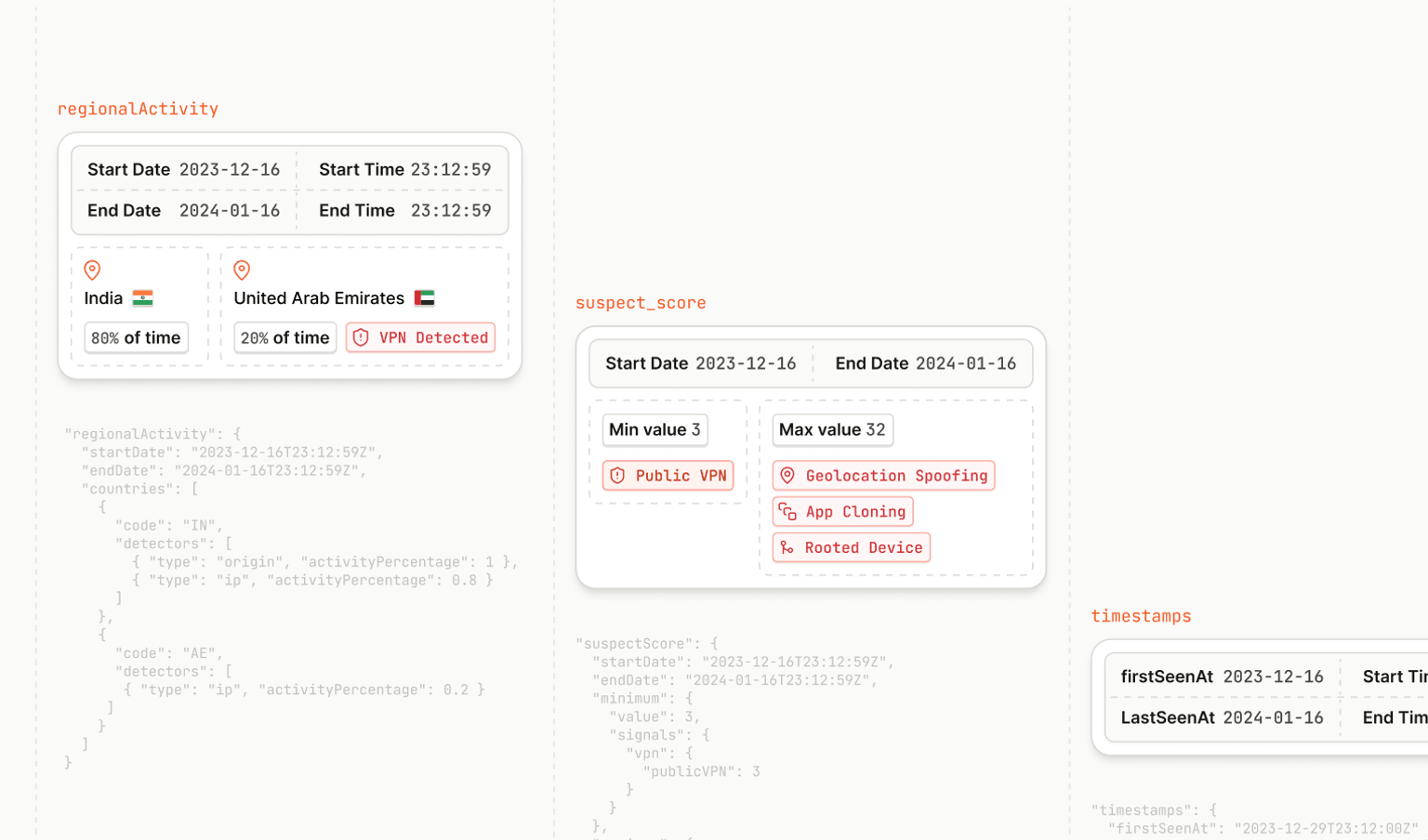
Fingerprint provides the device intelligence layer that makes the controls above actionable. At its core, Fingerprint delivers a stable visitor identifier that recognizes returning browsers and devices even when cookies are cleared, VPNs are in use, or a user is browsing in incognito mode. This persistence is what makes device binding reliable: the identifier stays consistent across sessions, so a fraudster logging in from their own device will produce a visitor identifier that has never been associated with the target account.
In addition to identification, Fingerprint's 20+ Smart Signals surface additional context for each visit. VPN detection flags anonymized connections, bot detection identifies automated behavior like programmatic OTP submission, and browser tamper detection catches modified or spoofed browser environments.
Because Fingerprint is API-first, it easily slots into existing authentication flows. Device context is available the moment a user arrives, even before any credentials are submitted, which means it provides a signal exactly at the point in the flow where this attack needs to be caught.
Going beyond OTP
Phishing APK fraud succeeds because it works within the rules of conventional authentication. The credentials are real, the OTP is valid, and nothing in the traditional flow raises a flag. What it can't fake is the device.
Adding device intelligence to your authentication stack closes a gap that credentials and OTPs can leave wide open. Combined with stronger authentication methods and a clear device binding strategy, it gives you a way to catch fraud that has already learned to look legitimate.
If you want to see how Fingerprint's device intelligence fits into your existing flow, you can start a free trial or reach out to our team to talk through your use case.
Frequently Asked Questions
What is a phishing APK?
A phishing APK is a malicious Android app distributed outside official app stores, typically through social engineering lures like fake bonus offers or account verification tools. Once installed, it can silently read SMS messages and forward them to attackers without any knowledge or further action from the victim.
How do fraudsters intercept SMS OTPs?
Fraudsters trick victims into installing a malicious app that requests SMS read permissions. When a legitimate app sends an OTP, the malicious app reads it the moment it arrives and forwards it to the attacker in real time, allowing them to complete a fraudulent login from their own device.
How does device intelligence differ from two-factor authentication?
How does device intelligence differ from two-factor authentication? Two-factor authentication verifies what a user knows and has. Device intelligence adds context about the device itself, including whether it has been seen before, whether it shows signs of tampering, and whether the session behavior looks human. It works alongside authentication rather than replacing it.