Summarize this article with
Every fraud and risk team asks a version of the same question: What does normal traffic actually look like? They're not looking for theoretical baselines, but real measures of what people do when they hit decision points — signups, logins, checkouts, account recovery.
We created the 2026 Fingerprint Device Intelligence Report to answer just that. It's our inaugural annual report, looking at device and browser characteristics drawn from more than 23 billion identification events across over 7 billion browsers and devices worldwide. Some of it might confirm what you expect, but a few findings might change how you think about your risk model.
The overall trend you'll see is that risk concentrates in specific environments. While desktop (especially Chromium-based browsers) is where most of the action is, when risk signals do appear on mobile, they tend to carry more weight. You'll also see how behaviors once considered niche, like VPN usage, have become part of the baseline, and where evasion techniques are actively on the rise.
If you want to know what real traffic looks like at decision points, this report is your baseline. Let's get into it.
VPN usage is the new normal
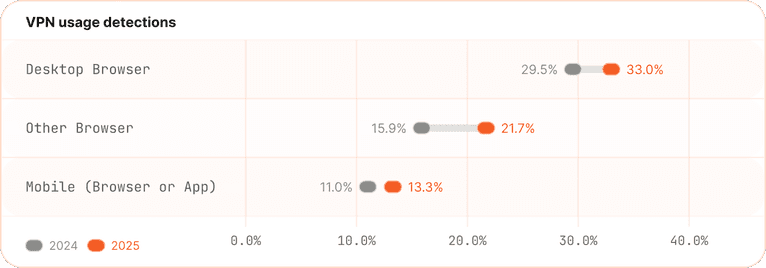
In 2025, roughly 1 in 5 identification events involved VPN usage, up from about 1 in 6 the year before. For Chromium-based desktop browsers, that climbs to 1 in 3. Even on mobile, 13% of identification events involve VPN routing, up from 11% in 2024.
The drivers are likely a mix of general privacy awareness, expanded enforcement of age-verification laws like the UK's Online Safety Act pushing users to route around geo-restrictions, and the simple fact that VPNs have gotten more well known and easier to use. Among named browser segments, iOS Safari saw the largest year-over-year jump — from 10% to 15% — a sign this isn't just a desktop power-user behavior.
For most teams, VPN presence is useful as context, and shouldn’t be used to determine whether a visitor is suspicious. That said, there are industries where VPN restrictions are a legitimate business requirement, such as content streaming, gambling, and other areas where geo-compliance matters. In those cases, the data here is useful for calibrating expected friction, not eliminating the check.
Desktop browsers are the primary battleground for fraud
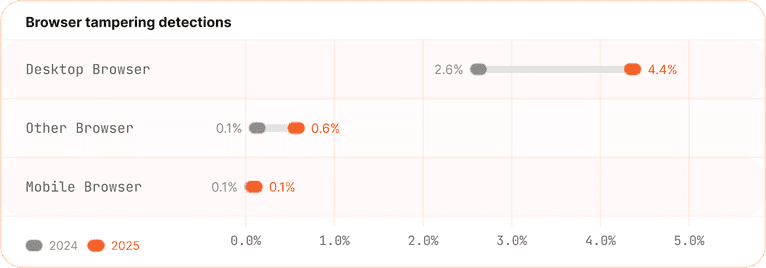
If you want to understand where sophisticated fraud actually lives, look to the desktop. The signal distribution across desktop browsers is unlike anything you see on mobile: in 2025, 4.4% of desktop browser identifications showed browser tampering techniques designed to confuse weaker fingerprinting systems, up from 2.6% in 2024. That's not a huge absolute number, but nearly doubling year-over-year is a meaningful trend. Chromium-based desktop browsers account for the bulk of it at 4.8%.
Tampering isn't the only thing accumulating on desktop. Virtual machines showed up in 13% of Chromium desktop identifications in 2025, and developer tools were open in 6% of desktop browser sessions. Any one of these signals on its own could reflect a developer doing their job. When they stack together on the same session, you're looking at something more suspicious.
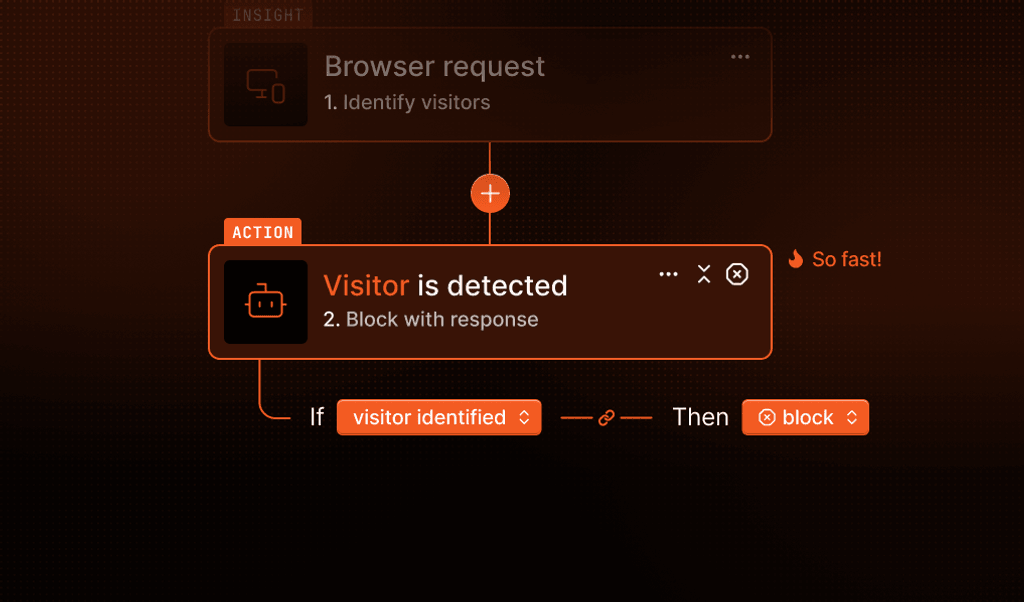
Automation tells a similar story. Bot activity reaching protected workflows is a small slice of overall traffic, but it's highly concentrated on desktop, and the portion associated with abusive behavior is substantial. It's worth noting that this data reflects automation that passes both network-level filtering and Fingerprint's own search and AI bot filtering. What remains is the harder-to-detect, purpose-built automation designed to evade controls. That's the slice that actually matters for fraud teams.
What the data does make clear is that desktop is where your enforcement effort has the highest return. Mobile fraud signals are rarer but more meaningful when they appear. Desktop is the opposite: noisier, more complex, and where the majority of sophisticated abuse is concentrated.
Mobile: fewer signals, but clearer ones
Mobile app traffic tells a different story from desktop traffic. The tighter constraints of native mobile environments mean that most of the modification and evasion techniques common on desktop simply aren't practical. The result is a much cleaner baseline, and that cleanliness is exactly what makes mobile risk signals valuable when they do appear.
Across the mobile integrity signals we identify in native app traffic, the numbers are small across the board. Rooted Android devices accounted for 0.12% of identifications in 2025, jailbroken iOS devices for 0.03%, Android emulators for 0.37%, and app cloning for 0.16%.
Small percentages, but with billions of mobile device identifications in the dataset, even fractions of a percent represent millions of events. These aren't signals you'll be managing at scale, but when they surface, they're meaningful precisely because they're rare. A rooted device or an emulator showing up during account creation or checkout carries much more weight than someone using a VPN on a desktop.
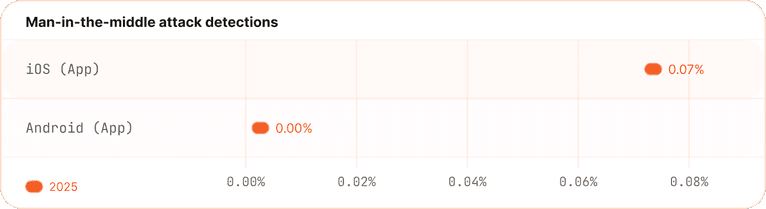
One signal worth calling out specifically is the presence of man-in-the-middle attacks. 0.07% of app identifications on iOS showed MitM characteristics in 2025. Unlike other integrity signals, this one specifically detects when communication between the app and Fingerprint servers is being intercepted, potentially to observe, modify, or block requests in real time. It's a new signal for us (detection went live in March 2025), and the absolute number is small, but it represents a more deliberate and technically involved form of interference than other mobile integrity indicators.
Unlike desktop, where risk signals often need context and combinations to be actionable, a single strong mobile integrity signal can carry enough weight to justify a response on its own.
What these trends mean for your strategy
If there's one thing this data makes clear, it's that what counts as normal traffic has shifted.
VPNs are now a routine part of how people browse, and as AI agents become more common doing legitimate work on behalf of users, the programmatic browser patterns fraud teams have historically treated as red flags are worth re-examining. The line between "power user" and "abusive automation" is getting harder to draw from a single signal.
This doesn't mean fraud is getting easier to hide. Most traffic still looks exactly like what it is. Looking at our Suspect Score, which combines the weight of all signals triggered for a given identification event, 67% of all 2025 traffic scored in the lowest bucket, and 85% fell below a score of 10. The vast majority of traffic triggers no meaningful signals at all.
But the context required to correctly interpret what falls in the gray zone is increasing. A session running in a VM with developer tools open could be a QA engineer, an AI agent completing a task, or someone running an account takeover script. The behavior looks similar on its own. The difference tends to show up when you look at the full picture.
The good news is that high-risk sessions, the ones where multiple uncommon signals stack together, remain genuinely rare. Less than 4% of traffic in 2025 scored above 20 on the Suspect Score. That rarity is what makes them findable. The goal isn't to treat every unusual signal as a threat. It's to know your traffic well enough that the things worth acting on are obvious.
Dig into the data
This post covers the highlights, but the full report goes much deeper. You'll find breakdowns by region, platform, and browser runtime, plus key takeaways for product and fraud prevention teams.
If you're building or refining your fraud strategy, it's worth knowing what the traffic hitting your decision points actually looks like. Read the 2026 Fingerprint Device Intelligence Report to get the complete picture.
FAQ
In 2025, roughly 1 in 5 identification events involved VPN usage. On Chromium-based desktop browsers, that figure climbs to 1 in 3. VPN usage is no longer an edge case and should not be treated as inherently suspicious in most cases.
Browser tampering refers to techniques used to modify or obscure browser characteristics, such as spoofing identifiers or using anti-detect browsers, to evade fingerprinting systems. In 2025, 4.4% of desktop browser identifications showed tampering, nearly double the 2.6% rate in 2024.
Mobile environments have tighter technical constraints that make many evasion techniques impractical, resulting in lower overall rates of risk signals. However, when signals like rooted devices, emulators, or app cloning do appear on mobile, they tend to be stronger indicators of risk than equivalent signals on desktop.