Summarize this article with
Introduction
As of 2021, there are over 3 Billion active Android users worldwide. With such a massive network of mobile devices, fraudsters actively seek ways to exploit the most vulnerable of these billions of devices. Two common methods involve utilizing Android emulators and tampering with Android devices, or preying on already tampered devices.
On one hand, Android emulators have revolutionized the way developers and enthusiasts interact with Android apps and games. However, while initially designed for legitimate purposes such as app testing and gaming, bad actors have co-opted emulators for nefarious activities. Additionally, for mobile app developers and website owners, understanding the concept of Android tampering is crucial to protecting their products from breaches and malicious attacks.
This blog post aims to shed light on these two concepts, offering insights into the different types of Android emulators and tampering methods, how they work, why businesses should detect if these types of Android devices are visiting their website, and how device intelligence can help with this detection.
Android emulators
What is an android emulator?
Android emulators allow users to simulate an Android device on their computer. They mimic the functionality of a physical Android device, enabling users to run Android applications without needing a dedicated device. In most cases, the purpose of Android emulators is to provide developers with a convenient and efficient way to develop, debug, and test their applications.
With an android emulator, developers can access a controlled pre-production environment to simulate various device configurations, screen sizes, and Android versions. The controlled environment allows developers to identify and fix issues or bugs before deploying their applications into production. For many organizations, Android emulators are a standard operating process and play a crucial role in the Android development process, allowing developers to create high-quality and reliable applications for the Android platform.
What are some of the good Android emulators available today?
When testing and developing Android applications, having a reliable emulator is crucial. One popular option is Google’s native Android Emulator, which offers a wide range of features and supports various Android versions, allowing developers to test their apps on different devices. The Google Android Emulator also integrates with Android Studio, making it a preferred choice for many developers building and maintaining Android mobile applications.
Another noteworthy emulator is Genymotion, which provides a virtual environment to run and test Android apps. It offers a high-performance experience and supports advanced features like GPS simulation and multi-touch gestures.
For developers seeking a cloud-based solution, Google Firebase offers Test Lab, which allows developers to test their applications on real devices in a Google data center. The difference between Google’s native emulation and Test Lab is that with Test Lab, you can test on a wide range of both Android and iOS devices with easy scalability.
What are the use cases for using android emulators?
As mentioned, Android emulators provide great value and benefit to mobile application developers looking to test and iterate on their applications before releasing them to production. Developers can quickly switch between virtual devices, making testing their applications on various instruments and screen sizes easier. Additionally, emulators can provide performance profiling tools and simulate various network conditions, helping developers optimize their apps for different scenarios.
How are android emulators used for fraud?
However, the fact that Android emulators are so flexible and versatile means they also have the potential for misuse. Fraudsters now leverage them for activities ranging from click fraud in mobile games to large-scale financial fraud operations.
Popular Android emulators such as Nox, BlueStacks, and MEmu have been implicated in fraudulent activities. Fraudsters often hide these emulators using sophisticated techniques like altering device identifiers, spoofing IP addresses, or even simulating human-like interactions.
How to detect Android emulators:
The main method of detecting Android emulators involves identifying anomalies that separate them from genuine devices. These anomalies may include:
- Inconsistencies in device properties: Emulated devices often exhibit discrepancies in system properties.
- Behavioral anomalies: Emulators may demonstrate unusual user behavior, such as high-speed clicks or repetitive patterns.
- Network indicators: Multiple requests originating from the same IP address could indicate emulator use.
Failure to detect and prevent against emulator-based fraud can lead to significant consequences, including financial losses, reputational damage, and compromised user data.
Android tampering
What is android tampering?
Android tampering occurs when there’s an unauthorized alteration or modification of an Android operating system or application, usually by hackers with malicious intent. Fraudsters often orchestrate these alterations to exploit vulnerabilities for malicious activities such as data theft, spreading malware, or manipulating app functionalities. It significantly threatens device and application integrity, user privacy, and data security.
On top of that, it’s a widespread concern for most Android devices. According to NowSecure, 82% of Android devices were susceptible to at least one out of 25 vulnerabilities in the Android operating system.
Android tampering can lead to severe consequences for mobile applications, including loss of user trust, brand reputation damage, legal implications, and financial losses. It can also compromise user data, leading to identity theft, fraudulent transactions, and privacy invasion.
What are the common Android tampering methods?
- Counterfeit App Publishing: This involves creating a replica of an existing app and uploading it to the Play Store. The cloned app often contains malicious code to steal user data or infect devices with malware.
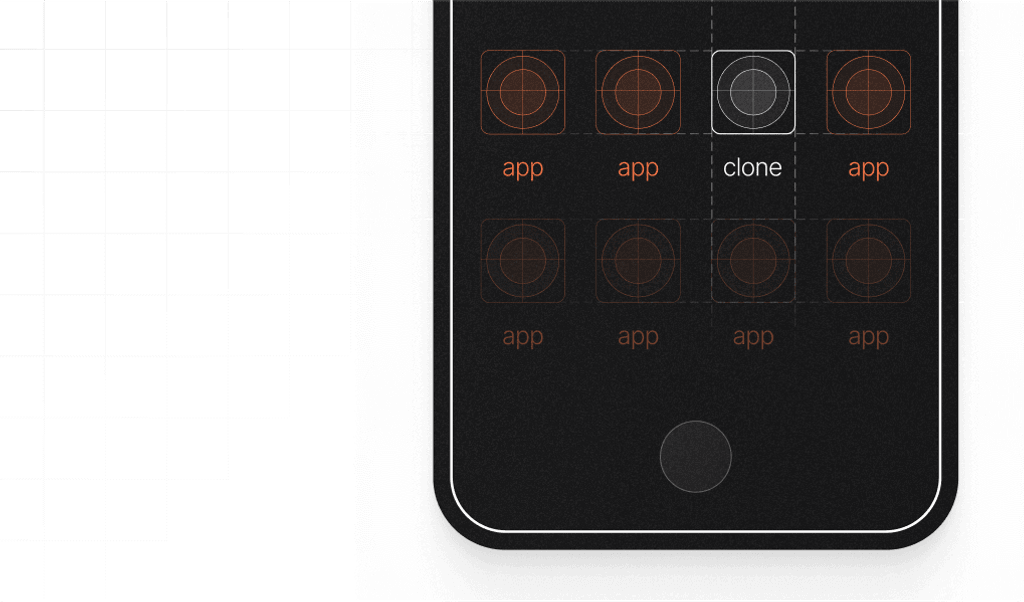
- On-Device App Cloning: Users create multiple instances of a legitimate app on a single device to simulate different user accounts making it appear as though multiple different users are engaging with the app.
- Rooting: Rooting an Android device grants privileged control over its operating system, bypassing manufacturer restrictions. Fraudsters use rooting to disable security features, install malicious apps, and simulate multiple fake accounts to evade detection systems.
- Reverse Engineering: Hackers decompile the app's binary code to understand its structure and expose and exploit vulnerabilities.
- Code Injection: Hackers inject malicious code into the app, altering its functionality or compromising security.
- Unauthorized Repackaging: Original apps are repackaged with additional malicious components and redistributed through third-party app stores.
Why do fraudsters use Android tampering as a strategy to commit fraud?
Fraudsters primarily tamper with Android devices and mobile applications with the potential goals of gaining unauthorized access to sensitive information, spreading malware to execute a future large-scale automated bot attack, or exploiting vulnerabilities in the app code. If a fraudster is able to successfully access a tampered Android device, they can access information
Anyone one of these can cause be costly not only to the device holder and app user but also to any affected application developers.
What are the signs that indicate an Android device has been tampered with?
As an Android device user, there are indicators that an Android device has been tampered with, however subtle, but if you know what to look for, you can spot them. Here are some of the most common indicators:
- Unexpected Battery Drain: If your battery drains much faster than usual, it could be a sign that a malicious application is running in the background.
- Increased Data Usage: A sudden spike in data usage can indicate that your device is sending information to a third party.
- Poor Performance: If your device is consistently slow or crashing, it may be due to a malicious application using up system resources.
- Strange Pop-Ups: Even when using an ad-blocker, persistent pop-ups could indicate a malware infection.
- Unwanted Applications: If you find applications you didn't install on your device, your phone may have been tampered with.
- Odd Phone Behavior: If your phone behaves strangely, such as turning off and on by itself, making unusual noises, or if you notice apps opening and closing without your input, these could all be signs of tampering.
- Suspicious Activity: If you see activities on your phone that you didn't do, like calls you didn't make, texts you didn't send, or emails you didn't write, it's likely your phone is compromised.
Preventing fraudulent activities from Android emulators and tampered Android devices:
The key to stopping nefarious activities originating from Android emulators or tampered devices is to prevent them from being able to take any action on your site or within your application, to begin with.
You want to employ the most modern development tools and practices and keep them updated regularly, including conducting regular security audits to identify potential vulnerabilities within your applications and remedy them promptly. Additionally, you’ll want to encrypt any protected information even if the application becomes compromised.
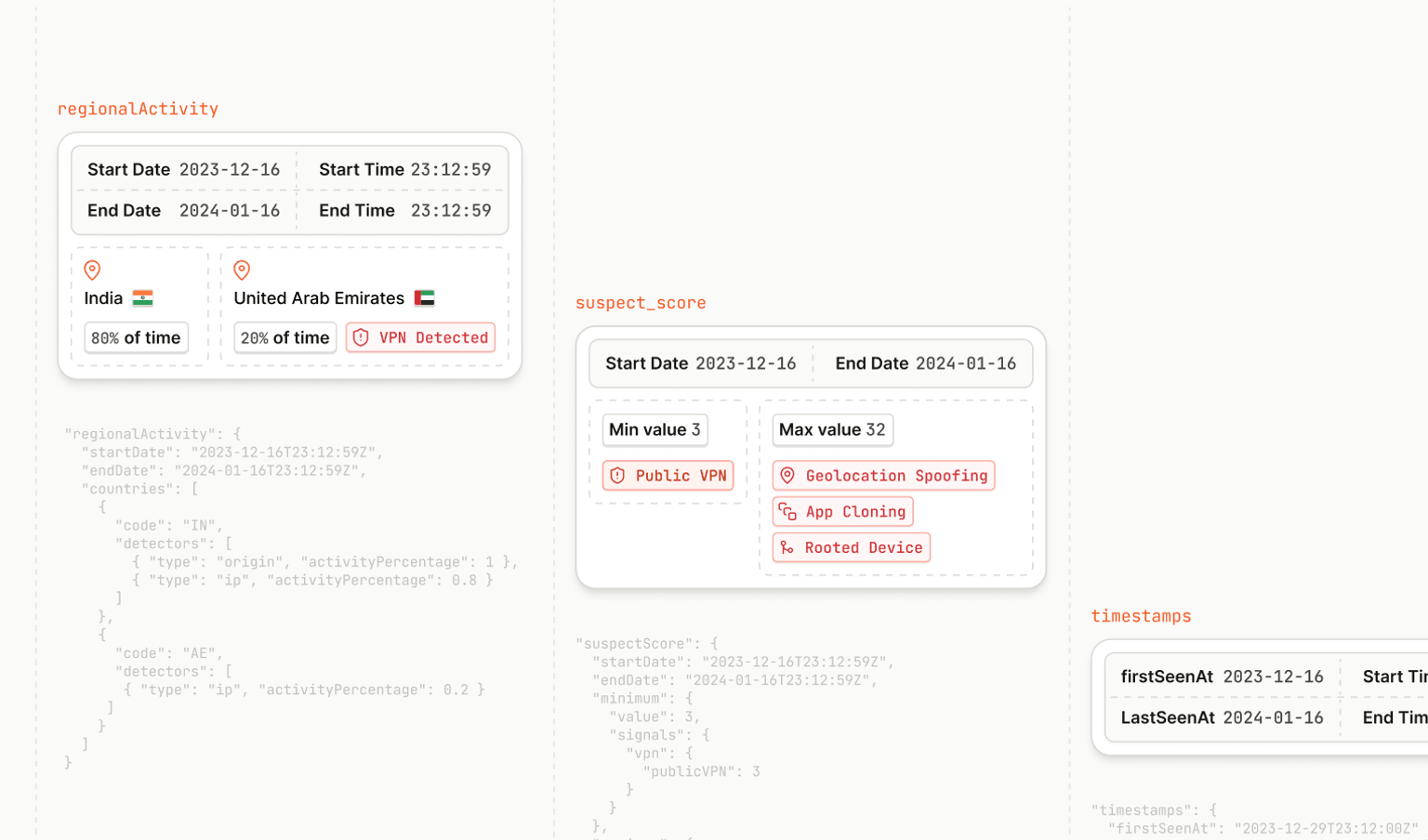
Lastly, you should implement fraud detection and prevention strategies that can accurately identify returning devices repeatedly and alert you to mobile device tampering. Device intelligence platforms, such as Fingerprint, can offer a robust set of Smart Signals to aid in highly accurate device identification. Specifically, mobile signals such as Android emulator detection, rooted device detection, and on-device cloned app detection can help you to better protect your apps and legitimate users.
Frequently Asked Questions
What are some specific signs or indicators that an Android emulator is being used for fraudulent purposes?
Detecting an Android emulator used for fraudulent purposes can be challenging as fraudsters often try to make the emulator seem like a legitimate device. However, there could be some signs to look out for. These include repeated actions executed with unusual precision or speed, or numerous actions coming from what appears to be the same device but with different user accounts. Other technical indicators might involve checking the device's hardware properties, as emulators often have hardware configurations that are different from typical Android devices.
How can individuals protect their personal Android devices from tamper fraud?
As for protecting personal Android devices from tamper fraud, it's essential to be cautious when installing apps, especially those from third-party sources. Only download apps from trusted platforms like Google Play Store and always check reviews and ratings before installation. It’s also crucial to regularly update your device's software, as updates often include security patches that prevent fraudsters from exploiting vulnerabilities.
Apart from gaming and fraud, are there any other prominent applications of Android emulators?
Android emulators are not just used for gaming and fraudulent activities. They are also widely used in app development and testing. Developers use emulators to test the functionality and performance of their apps across different devices and Android versions without needing to have the physical devices. This aids in identifying any device-specific issues or bugs before the app is released to the public.