![[Tutorial] What Is SMS Fraud? How to Detect and Prevent SMS Pumping Fraud [Tutorial] What Is SMS Fraud? How to Detect and Prevent SMS Pumping Fraud](/static/3bcefa86adfb1f403f6a5d349047275b/9e18a/blog_sms_fraud_tutorial.png)
Summarize this article with
Text messaging has become a crucial communication channel for businesses to reach customers regarding account information, updates, and content. However, as the popularity of Short Message Services (SMS) increases, so does the risk of SMS fraud. Fraudsters are finding new ways to exploit SMS to steal money or sensitive information from organizations. In the business world, this fraud usually focuses on compromising security measures like SMS-based one-time passwords (OTP) used for authentication.
In this article, we will explore the issue of SMS fraud from a business perspective. What exactly is SMS fraud, and how does it impact companies? We will cover the most common types of SMS fraud businesses must be aware of to identify risks and abnormalities in SMS use. Most importantly, we will discuss measures companies can take to detect and prevent SMS fraud.
What is SMS fraud?
SMS fraud refers to illegal activities conducted through text messaging services. This form of fraud manipulates SMS, a widely used communication channel, to achieve various nefarious objectives. The methods range from sending deceptive messages to users to orchestrating complex schemes that exploit business processes. The common goal across these methods is to gain unauthorized access to resources, steal personal information, or incur financial losses for victims.
Common types of SMS fraud
Some of the most common types of SMS fraud that businesses should be aware of include:
SMS Pumping Fraud
SMS pumping fraud involves sending massive volumes of messages, often automated, from a single device. A typical scenario is a fraudster setting up a system to incessantly send messages to premium-rate numbers they control, thereby generating substantial charges. For businesses, this can lead to inflated SMS costs and depleted resources. Fraudsters pursue this for monetary gain, exploiting the pay-per-message billing structure often used in SMS services.
Subscriber Identity Module (SIM) Swapping
In SIM swapping, fraudsters deceive telecom operators to reassign a victim's phone number to a new SIM card, usually in their control. Once successfully controlled, they can intercept text messages, including OTPs for banking and other secure services. By accessing these OTPs, they can bypass security measures and access sensitive accounts, leading to identity theft or financial fraud.
Phishing via SMS (Smishing)
While a more personal attack, smishing uses deceptive texts that mimic legitimate entities, urging recipients to reveal personal data or click on malicious links. An example is a message posing as a bank, asking users to confirm account details or view an urgent notice via a provided link. The objective here is typically identity theft or the installation of malware for further exploitation.
The impact of SMS fraud on businesses
SMS fraud has significant consequences beyond the immediate financial losses victims suffer. It is not solely about safeguarding financial assets but also about preserving the integrity of personal and corporate digital identities. Businesses and individuals face numerous risks when it comes to fraudulent SMS activities, including:
- Financial Losses: Businesses face inflated SMS costs due to SMS pumping, reimbursement expenses for affected customers, and potential fines for security breaches. For individuals, SMS fraud can lead to unauthorized charges, drained bank accounts, or stolen credit card information. These financial burdens can be substantial, affecting the bottom line of companies and the personal finances of individuals.
- Trust Erosion: Trust is a fundamental element in the relationship between businesses and customers. When customers fall victim to SMS fraud through a company's communication channels, it can erode this trust. Recovering from such reputational damage often requires significant time and resources.
- Compromised Security and Privacy: SMS fraud tactics like SIM swapping and smishing directly target the privacy and security of individuals, leading to identity theft and unauthorized access to sensitive information. For businesses, these breaches can mean exposure of customer data, violation of privacy laws, and loss of intellectual property.
- Operational Disruptions: Dealing with the aftermath of an SMS fraud attack can disrupt regular business operations. Companies must redirect resources to address security breaches, handle customer complaints, and upgrade security measures. This shift in focus can detract from a business's core operations and growth.
- Regulatory and Legal Consequences: Businesses may face legal challenges and regulatory scrutiny following an incident of SMS fraud, especially if customer data is compromised. Compliance with data protection laws means firms are obligated to safeguard customer information. Failing to do so can lead to hefty penalties.
Detecting and Preventing SMS Fraud
Understanding and mitigating SMS fraud is vital to safeguarding individuals and businesses from its harmful effects. A well-rounded approach, which includes the use of technology, increased awareness, and ongoing diligence, can significantly reduce susceptibility to such deceptive activities. Battling SMS fraud requires varied approaches using suitable tools and best practices to build a strong defense against these threats.
Some measures businesses can implement include:
SMS Message Limits
Set limits on the number of SMS messages sent to a single device within a specific timeframe to prevent SMS pumping fraud. Companies can deter fraudsters while maintaining a balance that does not impact genuine users by requiring additional verification methods when visitors exceed this limit.
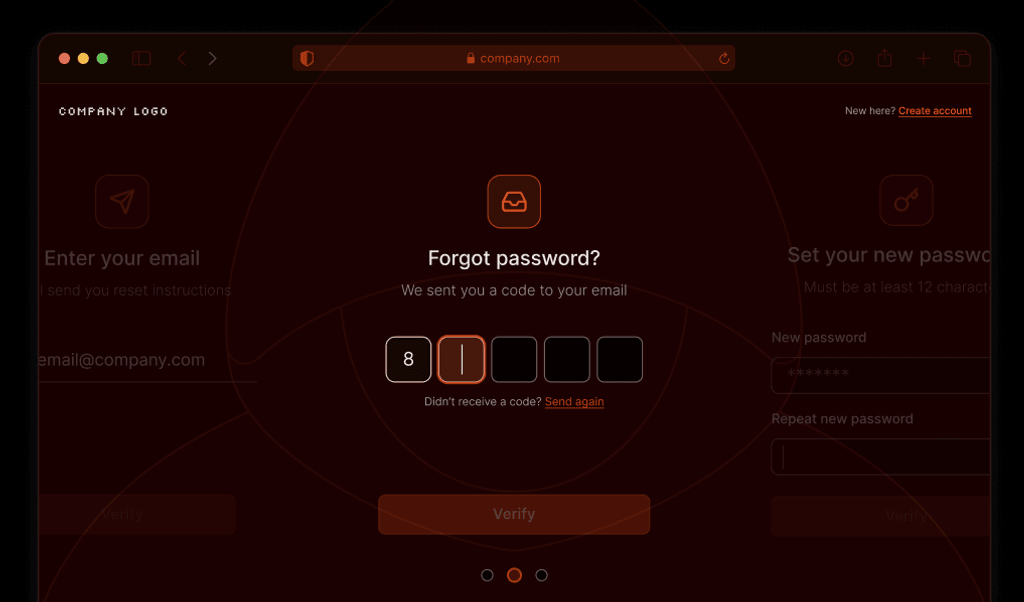
OTP Cool Downs
Implement a cooling-off period for SMS verifications, like OTPs, using device identifiers and attributes to differentiate between new, returning, and suspicious devices. Businesses can bypass SMS verification for known users with a recent history of safe interactions identified through their consistent device identifiers. For new devices, send SMS messages as usual; for suspicious devices, add additional verification forms. This approach not only streamlines the user experience for regular users but also protects against fraudulent access attempts, all while cutting down SMS costs and the potential for SMS fraud.
Account Linking
Assign a unique device identifier to each visitor and monitor which devices access multiple accounts. Accessing numerous accounts from a single device is common in SMS pumping fraud or account takeover schemes. By detecting and analyzing account access patterns linked to a single device, businesses can flag suspicious activities and initiate additional security checks or block access when necessary to prevent SMS fraud.
Bot Detection
Check if humans or bots are initiating SMS requests from your service. By only allowing human-based requests within your SMS-related services, businesses can prevent using automated bots, often behind large-scale SMS fraud attempts like SMS pumping. Once a bot is detected, the system can either completely block SMS services to that visitor or impose throttling measures, significantly reducing the SMS request rate.
Risk Analysis
Evaluate the potential risk of visitors by analyzing device attributes, including whether they are using a virtual machine, a privacy-oriented browser like Tor, or accessing your site from a location you do not operate in. Certain attribute combinations and signals can indicate potentially malicious intent. With this risk profile, businesses can tailor their response to SMS requests, from requiring additional verification steps for high-risk profiles to allowing seamless access for low-risk visitors.
Monitoring and Analytics
Monitor and track your SMS request traffic to find patterns or unusual behavior. When anomalies are detected, like sudden spikes in SMS requests from a single device, it's a potential red flag for SMS pumping or spamming. From there, you can investigate the source, pinpointing whether it's a specific number or location, and block SMS requests from that device if deemed suspicious.
User Education
Educate users on recognizing and responding to suspicious messages, the risks of smishing, and the importance of not clicking on unknown links or sharing personal information via SMS. Regular training sessions or informational emails can keep users informed, making them a strong line of defense against SMS fraud.
Leveraging Fingerprint to combat SMS fraud
One of the top components in preventing SMS fraud is identifying the devices making the requests. Whether it's OTP messages or links to download your app, you only want to send these to legitimate users and prevent fraudsters from abusing them. Fingerprint's device intelligence platform helps businesses identify devices by analyzing over 70 identification signals and accurately identifying returning visitors.
[Want to see it in action? Try our interactive playground to see how Fingerprint helps fight SMS fraud.]
These visitor identifiers remain stable over months, allowing businesses to monitor long-term user behavior and identify unusual activity patterns. For instance, a single visitor identifier associated with multiple SMS verification requests from different numbers could indicate fraudulent activity, such as SMS pumping or account hijacking.
In addition to highly accurate visitor identifiers, Fingerprint Smart Signals provide additional information about visitor devices that can allow businesses to craft security rules and risk profiles. Real-time detection features, like browser tampering detection, bot detection, and geolocation spoofing, easily integrate into existing systems and allow for the creation of more secure authentication workflows.
Combining Fingerprint's visitor identifier with Smart Signals enables businesses to proactively protect against SMS fraud attempts, saving time and resources while providing a seamless user experience for legitimate visitors. Jumia, a leading African eCommerce platform, addressed over $40k in costs from SMS fraud by using Fingerprint to identify repeat visitors and prevent them from abusing their SMS verification system.
Step-by-step guide to detect SMS pumping fraud
Learn how to implement Fingerprint to prevent SMS pumping fraud
FAQ
One example could be that fraudsters might send messages claiming to be from a bank or other reputable organization, asking for personal information or directing the recipient to a phishing website.
In other cases, they might send a text message stating that the recipient has won a prize, but needs to pay a fee to claim it.
If an individual or business becomes a victim of SMS fraud, they should report it to their mobile carrier and local law enforcement authorities. They can also file a complaint with the Federal Trade Commission in the United States. Businesses might also want to notify their customers, especially if the fraudulent messages appear to come from their organization.
There are indeed laws in place to protect consumers and businesses from SMS fraud. In the United States, for example, the Telephone Consumer Protection Act regulates all forms of telemarketing, including text message spam. Violations of this act can result in hefty fines. Additionally, many countries have data protection and privacy laws that offer some level of protection against SMS fraud.
SMS pumping fraud involves sending a large volume of unsolicited messages through a network, often to exploit billing inefficiencies or to engage in spam or phishing activities.
Businesses can set SMS message limits, link accounts to unique device identifiers, and use bot detection strategies to mitigate fraudulent activities, ensuring effective use of OTPs for verification.