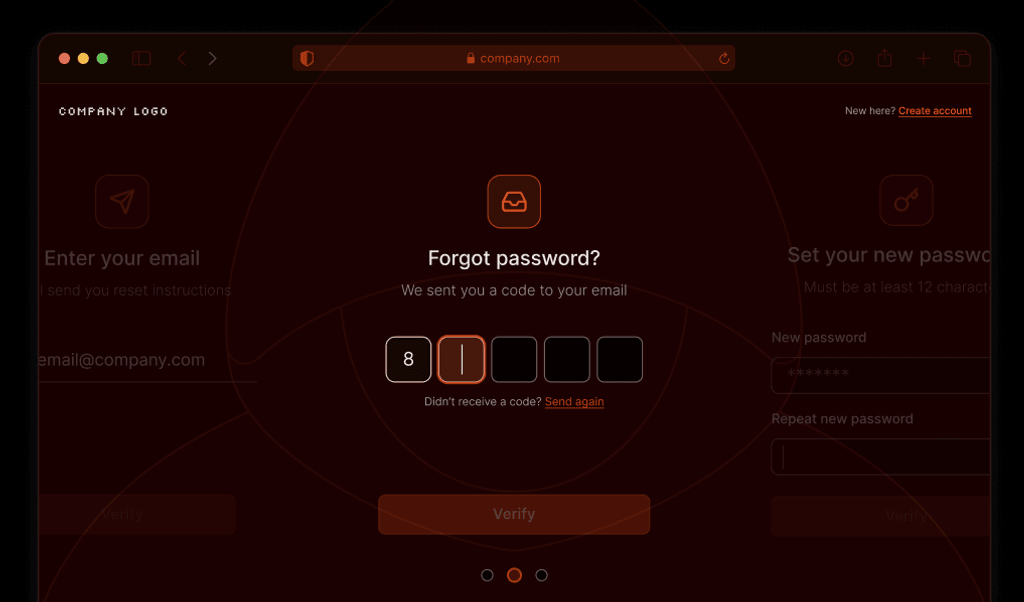
Summarize this article with
Has this ever happened to you? A while back, I logged into one of my streaming accounts (I won’t name names 👀), ready to finally watch a show I’d kept seeing a trailer for. I hadn’t logged in for a while, so I was surprised to find a bizarre recent watch history filled with titles I’d never even heard of. Luckily, the platform had a “recent devices” page that showed exactly when and where my account had been accessed. A quick glance confirmed it — I’d been hacked and someone had been watching obscure reality TV on my dime.
Even if with all the account security measures already in place, I was the one who caught the breach. And because the company gave me a window into my own account activity, I had the ability to act. Most businesses already work hard to keep user accounts safe, but giving users some visibility into their own activity adds an extra layer of protection. Whether it’s login alerts, device history, or unusual access warnings, these insights help customers spot suspicious activity.
To be clear, this doesn’t mean shifting the burden of account security onto users, as some previously breached companies have done 👀. We all know that humans aren’t the best at password hygiene or account security practices, and businesses should put measures in place to protect accounts without user input. But in addition to the security techniques you already (should) use, let’s look at how businesses can use user-facing security insights and transparency to build trust, strengthen account protections, and maybe even save a few streaming accounts along the way.
The business case for transparency in account security
Security transparency is more than just a nice-to-have. It can be a support ticket killer, a fraud prevention win, and a trust builder all rolled into one. Giving users insight into their own account activity doesn’t just make them feel more in control, it also saves businesses time and money.
Consider my personal streaming example. If I had no way to check my recent login history, guess where I was going? Straight to customer support. “Hey, I think my account was hacked. Can you check?” Now your team has to dig through logs, verify identities, and reassure me on account safety or confirm that my account had indeed been breached. All of this was avoided since I had access to a simple recent devices page.
My example was just for a media streaming site where, thankfully, the only thing negatively affected was my personal recommendation engine. However, the downstream effects of an account takeover can have significant financial consequences. Unauthorized purchases, money transfers, or subscription upgrades can have customers disputing charges, leading to lost revenue, chargebacks, and brand damage. Giving users early visibility into account security events helps catch suspicious activity before it escalates, reducing the risk of full-blown fraud cases.
This added transparency strengthens customer trust by giving them insight into their own account security. When users feel informed and in control, they’re more confident in the platform and less likely to switch to a competitor.
Core features of user-facing security insights
If you want to give users more transparency into their account security, what should you actually show them? You don’t need to dump an entire security log on them, but a few well-placed insights can help them spot suspicious activity. There are two main ways to implement this:
Persistent security views
The first category includes persistent security views where users can proactively check their account security at any time.
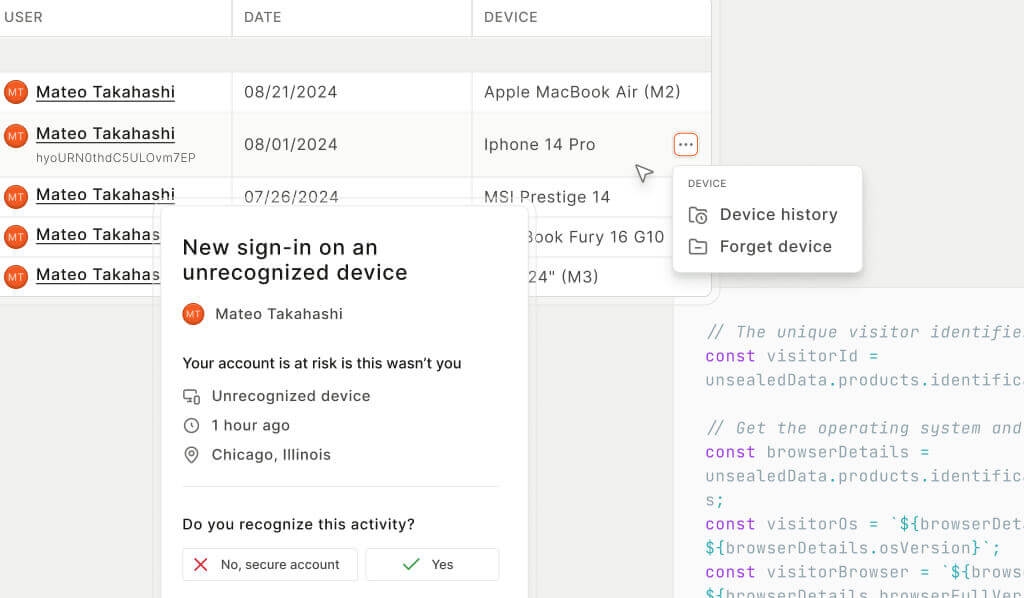
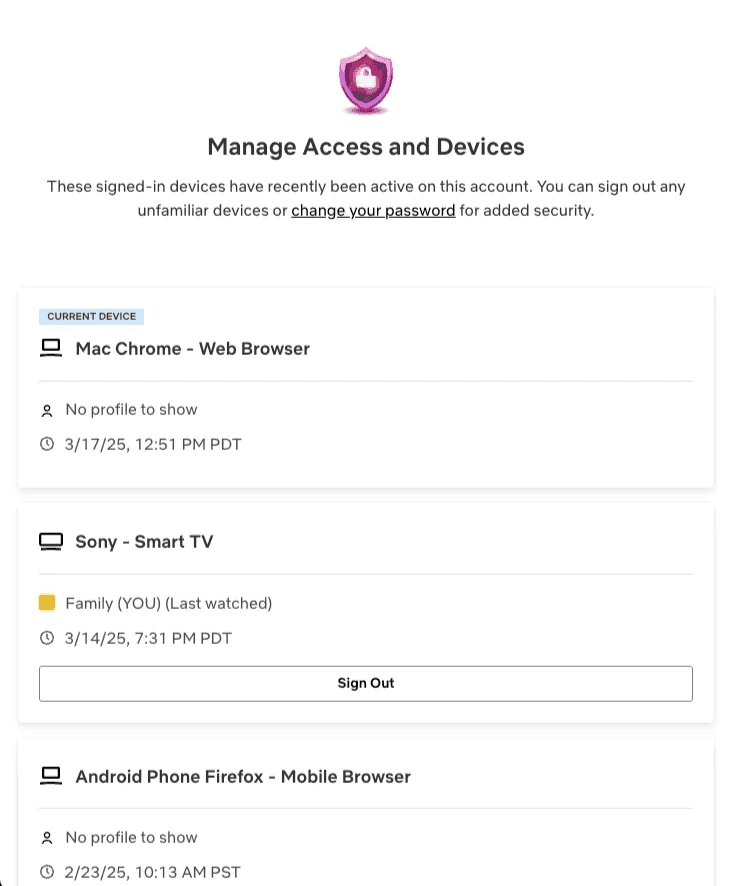
Recently used devices
Let’s start with the “Wait… that wasn’t me” page. Showing users a list of devices that have accessed their account, along with details like location, browser, operating system, and last active time, makes it easy to spot an intruder. Bonus points if you show which devices are currently logged in and let users log out unwanted sessions.
Linked accounts and third-party access
Users can sometimes link their accounts to other services, like third-party apps, OAuth connections, or social logins. Over time, these connections can be forgotten, leaving lingering access that users may no longer need or trust. Providing a clear view of linked accounts helps users manage their permissions, revoke outdated access, and reduce the risk of unauthorized third-party activity.
Security insights dashboard
These security views can also be combined into a summary dashboard, giving users a quick overview of their account security. This could include the last security setting change, recommendations like “Enable MFA for added protection,” and other key insights all in one place.
Real-time alerting
The second category is about keeping users in the loop on their account activity as it happens.
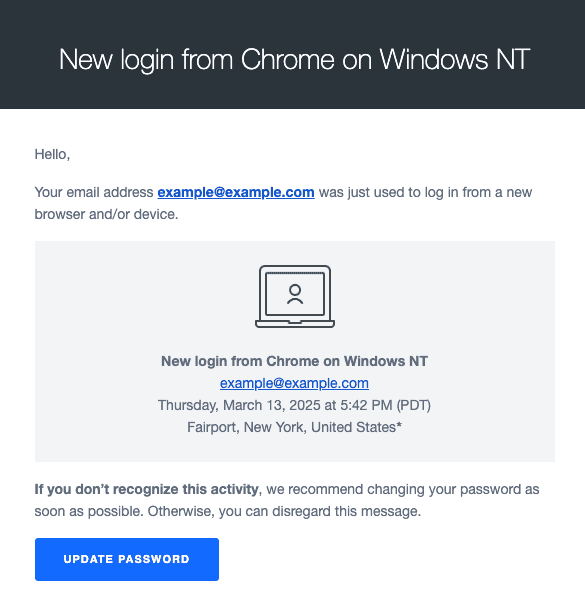
New device logins
A login from a new device or unexpected location might be harmless, or it might be someone who just bought a database of leaked credentials and is testing their luck. Giving users a heads-up when this happens lets them act fast if something seems off.
Failed login and MFA attempts
If someone is repeatedly failing to log in, that’s either a forgetful user or an attacker hammering their account. A quick notification lets users know when something suspicious is happening, especially if they weren’t the ones entering the wrong password five times in a row.
Sensitive activities
Changing a password? Updating an MFA method? Switching the delivery address on that cheese subscription? These might be normal actions or signs of a compromised account if they weren’t done by the user. Notifying users when key account details change gives them a chance to step in before it’s too late.
Best practices for designing account transparency
Now, how do you provide these insights without making users regret ever signing up for your service? Security alerts are great until they become an endless stream of notifications that users start ignoring. If you want this data to actually help customers, it needs to be useful, actionable, and not annoying so users will actually pay attention when it matters. Here’s how to get it right:
Be selective and don’t create unnecessary panic
Not every login needs a dramatic “Was this you?!” email. If users get a security alert every single time they sign in, they’ll start tuning them out or want to turn them off completely. Instead, focus on high-risk events like first-time logins on a new device, unusual locations, or impossible travel scenarios. Similarly, don’t treat a single failed login as a full-blown attack. Sometimes people just make typos.
Make insights clear, actionable, and easy to verify
A good security alert doesn’t just say, “Something happened.” It tells users exactly what happened and what to do next. Instead of a vague “New login detected” message, try “New login from Paris, France. If this wasn’t you, change your password and let us know.” Include useful details like device type, browser, location, and timestamp, and link directly to their recent devices page so they can quickly review their account activity without digging through settings. Also, if an alert is for a login that was them, give them an easy way to say “Yep, that was me.”
Give users control of their notifications
Security notifications are important, but that doesn’t mean they all need to be delivered the same way. Let users choose their preferred notification channels. Some may prefer email for login alerts, while others might want push notifications or text messages. The key is to ensure critical alerts always reach them while allowing flexibility for lower-priority ones.
Keep alerts consistent across platforms
If users get an email about a suspicious login, they should also see that information when they access your site or app. Showing security insights across platforms ensures users can access them wherever they interact with your service, increasing visibility and helping to confirm the message is legitimate rather than a clever phishing attempt.
Empowering users while strengthening security with device intelligence
These features don’t replace your core security measures, but by giving users visibility into their accounts with device history, login alerts, and security dashboards, you empower users to recognize and respond to potential threats before they escalate.
These insights build trust in your brand, help detect threats early, reduce fraud, and lighten support load. Ready to jump in and see how to give users this level of visibility and protection using device intelligence? Check out this step-by-step tutorial to see how you can detect devices and surface suspicious activity.
FAQ
Store device details like a unique device identifier, OS, browser, location, and timestamp for each successful login. Then display this data in the user’s account settings or dedicated recent devices page. Make sure to highlight the current device, and provide an option to sign out other sessions.
Providing users with access to their recent login activity helps them detect unauthorized access early, reducing the risk of account takeovers. It also builds trust, reduces support requests, and strengthens overall security by enabling users to take action when something looks suspicious.
Create a recent devices page and send real-time alerts for logins from new devices or locations, multiple failed attempts, or other high-risk actions. Present this information in a way users expect, providing clear details and actionable steps to help them secure their account.