Summarize this article with
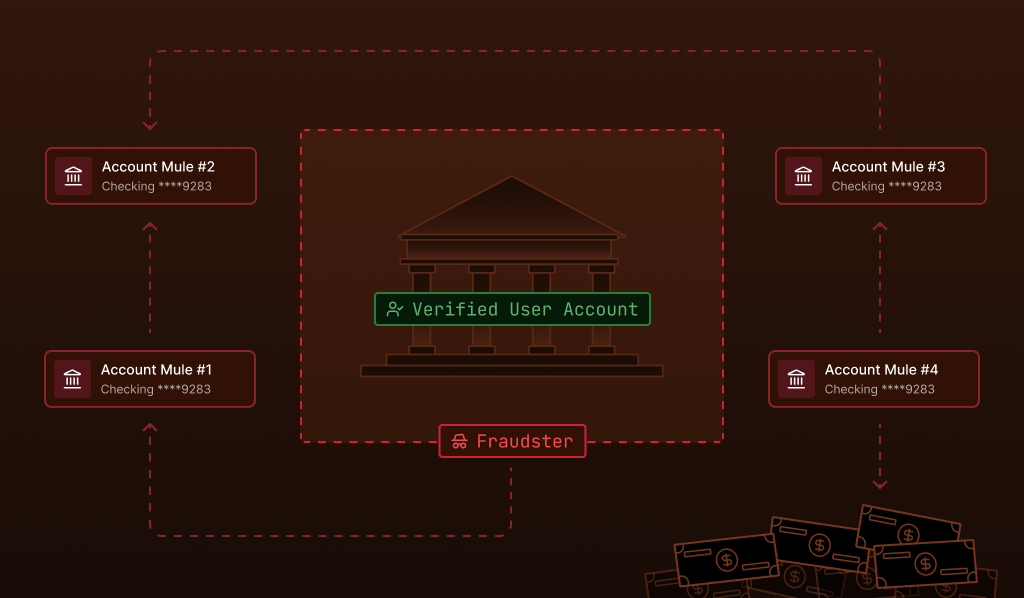
A newly opened bank account receives a $3,500 transfer. Minutes later, most of the money is sent to another account. Within an hour, the funds have moved again.
Individually, none of the transactions appears unusual. But when fraud teams review activity across related accounts, a pattern becomes clearer. Multiple accounts show the same behavior: rapid incoming transfers followed by immediate withdrawals or transfers to other financial institutions. The accounts may belong to different people, be held at different banks, and show no obvious connection, yet they all function as a single, coordinated machine.
This is mule account activity, a key component of modern financial fraud, and one of the most difficult threats for prevention teams to identify.
What is a mule account?
A mule account is a bank or financial account used by fraudsters to receive and transfer stolen funds. The person controlling the account, called a money mule, moves money between accounts, withdraws funds, or converts it into other forms, such as cryptocurrency. Mule accounts are typically used as go-betweens in money-laundering schemes: they sit between the point of theft and the fraudster’s final destination for the funds, making the money’s origin much harder to trace.
However, not all money mules play the same role. There’s a spectrum when it comes to how involved or aware they are. Some knowingly participate in exchange for a share of the proceeds. Others are deceived, responding to convincing job offers or social media messages that describe the work as simple payment processing. At the far end of the spectrum, some victims have had their accounts taken over without their knowledge.
Understanding this range matters for bank fraud teams: not every mule account holder is a criminal, and investigation and reporting strategies may vary by scenario.
How do mule accounts operate?
Fraud networks will orchestrate many mule accounts simultaneously, using them to receive, move, and ultimately obscure the origin of stolen funds.
The process typically unfolds in three stages.
Stage 1: Recruitment and access
Criminal groups recruit individuals through social media, online job boards, and messaging platforms, often targeting younger users with promises of quick income. Once recruited, these individuals hand over account credentials or actively participate in moving funds on instruction.
Increasingly, fraud networks are also purchasing access to compromised accounts on dark web marketplaces, bypassing recruitment entirely.
Stage 2: Layering
Once stolen funds enter a mule account, they’re quickly moved again, often within minutes, before fraud systems or investigators can intervene. The funds may pass through three, four, or more accounts in rapid succession, each transfer adding another layer of distance from the original theft. This process, known as layering, is a core technique in money laundering and is designed to defeat transaction monitoring systems that evaluate accounts in isolation.
Stage 3: Distribution
Rather than routing all funds through a single account, fraud networks spread transactions across many accounts simultaneously. Incoming funds are divided and sent to multiple destinations, each receiving an amount small enough to avoid triggering automated alerts. The suspicious behavior only becomes visible when activity across the full network is analyzed together.
Why mule accounts are difficult to detect
Detecting mule accounts is becoming more challenging as fraud networks grow in scale and sophistication. Data from the Banking & Payments Federation Ireland shows that nearly €9.4 million was laundered through mule accounts in the 12 months leading up to mid-2025, highlighting the scale of activity that financial institutions must monitor.
That figure reflects only detected and reported cases; the true volume of activity is almost certainly higher.
Several factors explain why detection remains so challenging.
Accounts pass standard onboarding checks
Mule accounts are often opened using real identities and genuine documentation. They pass identity verification and Know Your Customer (KYC) checks and may show normal activity for a period before being flagged for fraud. Traditional onboarding controls aren’t designed to catch accounts that are legitimate at the point of opening but fraudulent in intent.
The dueling challenge of transaction speed
In an active mule account scenario, funds will move through accounts in minutes. By the time a suspicious transaction is flagged by an automated system and reviewed by a human analyst, the money may have already passed through two more accounts at other institutions. The window for intervention is extremely narrow.
Meanwhile, financial institutions are working to speed up money transfers to make them more convenient for their customers—a dueling imperative that only makes it more difficult to stop mules. Any preventative measures or restrictions they place to try and slow down mule activity will end up slowing down legitimate transactions.
Transaction monitoring sees accounts, not networks
Conventional fraud detection evaluates individual accounts and transactions against rule-based thresholds. A single mule account receiving and forwarding $3,500 may not breach any threshold on its own. The fraud only becomes visible when the connections between accounts are mapped, something traditional transaction monitoring isn’t built to do.
How device intelligence helps identify mule accounts
Device intelligence addresses these gaps. By analyzing signals from the devices used to access a platform, fraud teams can identify relationships that account-level data alone would miss.
Shared device access
When the same device is logged into multiple accounts, then device intelligence captures that signal even if the accounts use different names, email addresses, and credentials. A single operator managing a network of 20 mule accounts from one laptop will leave a consistent device fingerprint across all 20 sessions, a pattern that is invisible to transaction monitoring but immediately apparent in device-level analysis.
Device reuse over time
Fraud networks often cycle through accounts, activating them for a short period and then moving on. Device intelligence creates persistent identifiers that survive session resets, browser clearing, and even some spoofing attempts. This means a device used to access a flagged mule account in January can be recognized when it accesses a new account in March, allowing investigators to connect historical and current activity.
Network-level clustering
Organized fraud operations sometimes run multiple devices within a shared environment, such as a single IP address, a common Wi-Fi network, a coordinated set of virtual machines, or a shared physical location. When device signals are combined with network, location, and behavioral signals, fraud teams can identify clusters of accounts that are linked at the infrastructure level, even when no individual account looks suspicious on its own.
Connecting signals to detect mule activity
Fingerprint’s device intelligence platform collects more than 100 signals from browsers, devices, and networks to generate a persistent visitor identifier. This allows organizations to recognize returning devices and surface connections between accounts that would otherwise remain hidden, giving investigators a starting point for network-level analysis rather than requiring them to discover mule rings one account at a time.
Fraud teams can also go a step further and combine several Smart Signals—like VM detection, proximity location, bot detection, and developer tool usage—in order to get a highly accurate lens to assess visitor intent and strengthen confidence in threat analysis.
Identifying mule accounts with Fingerprint
Mule accounts aren’t a new problem, but the infrastructure supporting them has grown much more sophisticated. Recruitment happens at scale online. Accounts are activated and abandoned quickly. Funds move across institutions faster than manual review processes can track them.
For fraud prevention teams, this means the question isn’t simply whether a transaction looks suspicious, but whether an account is connected to a broader pattern of coordinated activity. Device intelligence provides the layer of visibility needed to answer that question, linking accounts through shared devices, persistent identifiers, and network and device signals that transaction data alone can’t reveal.
For fraud teams, that means fewer mule accounts slipping through, and faster paths to identifying the networks behind them.
Start a free trial or contact our team to learn how device intelligence can strengthen your fraud detection strategy.