Summarize this article with
Introduction
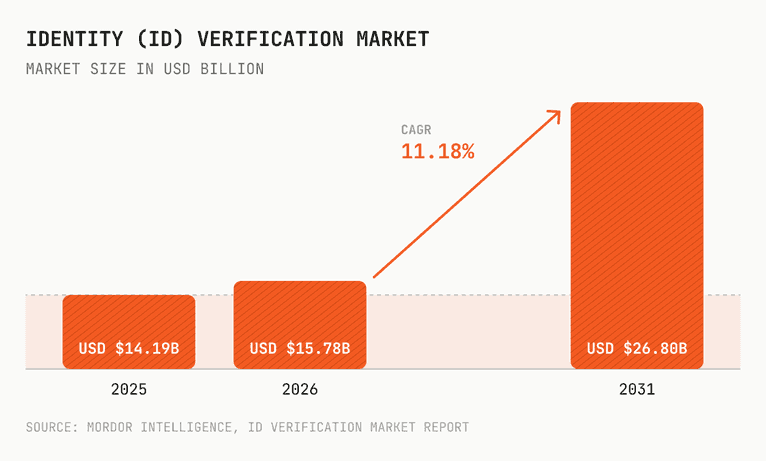
Identity verification is one of the fastest-growing segments in financial technology. In 2026, the global identity verification market is valued at $15.78 billion and is forecast to reach $26.8 billion by 2031.
Yet amid this massive growth, IDV platforms are facing a growing challenge. The capabilities of increasingly sophisticated attackers and AI-driven fraud are starting to outpace traditional, document-based identity checks. At the same time, everyday users are demanding faster, lower-friction experiences.
This report is a deep-dive into the ways fraudsters are exploiting gaps in identity verification flows, not just during onboarding, but before and after those moments in time. Plus, we'll share the important ways that persistent device intelligence can augment verification and help teams accurately assess risk, reduce blind spots, and maintain trust across the entire user lifecycle.
How generative AI broke the document-first verification model
The original identity verification model was built around a straightforward premise: Confirm who someone is at onboarding, issue a verified credential, and trust that credential for subsequent interactions. Physical document fraud was operationally difficult. Sophisticated forgeries required specialized skills, equipment, and materials, keeping the cost of entry high and the volume of attempts relatively low.
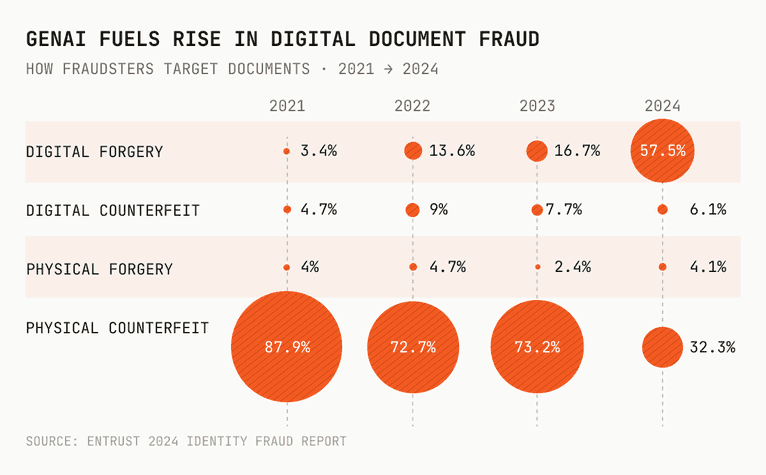
Generative AI changed the cost structure entirely. An estimated 42.5% of detected fraud events now involve generative AI, and commodity toolkits can produce near-perfect counterfeit passports for $30. Digital forgeries now account for 57.5% of all document fraud, a 244% year-over-year increase and a 1,600% increase compared to 2021.
Deepfakes account for 40% of all biometric fraud, and nine out of 10 off-the-shelf verification engines still misclassify sophisticated deepfakes in red-team tests.
The consequence for identity verification platforms is concrete: The document check alone can no longer serve as the primary basis for a trust decision. High-quality synthetic identity packages built from leaked personal data clear traditional checks when signals are evaluated in isolation.
Onboarding is just the beginning of fraud risk
Most identity verification systems were built to answer a single question at a single moment in time: Is this applicant who they claim to be? That question remains essential, but it’s no longer sufficient.
Fraud has moved to exploit the gaps that exist before and after that single moment. The industry is moving toward portable, reusable credentials that extend trust beyond the initial verification event. Yet a verified identity is only as trustworthy as the device presenting it, and many IDV platforms still lack a persistent read on the device.
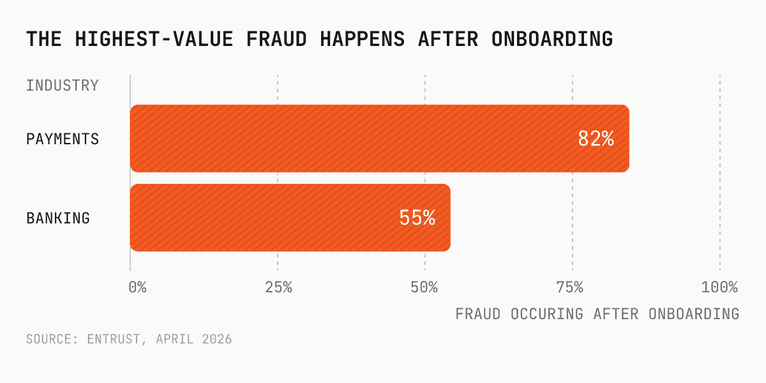
Fraudsters know this, too. The highest-value fraud schemes often begin after the initial verification is complete. In payments, 82% of fraud occurs after onboarding and is linked to account takeover fraud. In banking, that figure is 55%.
Traditional controls are evolving and creating new complexity
eIDAS 2.0 requires every EU member state to issue a Digital Identity Wallet within 24 months. Reusable identity credentials, portable digital identities, and transferable verified credentials are all pushing identity verification platforms to extend trust beyond the initial verification event.
That model only works if platforms can reliably recognize returning users without requiring a full re-verification flow. Yet many cannot.
This is the structural bind that the “verify once, reuse often” model creates. If the platform has to re-verify at every high-value moment—such as account recovery, payment updates, profile changes, and periodic Know Your Customer (KYC) refresh—then the platform also absorbs the frustrations and costs that come from added friction, churn, complaints, and operational strain. Trust the credential alone, and the platform accepts mounting fraud exposure from accounts whose ownership has silently changed.
Neither path is a viable long-term position at scale, and the gap between them widens as verification volumes grow. Without a persistent device identifier, a returning user is just a credential that showed up again. A verified email address, phone number, or identity token reappearing in a session does not explain who or what is behind it. A legitimate customer returning on a trusted device, a fraudster using stolen credentials, and a verified account that changed hands can look identical from the credential layer alone.
A persistent device identifier creates more clarity. Trusted returning users on a recognized device can move forward without re-verification. New or unusual environments can trigger scrutiny proportionate to the risk they represent.
The risks in identity verification for financial institutions
62% of banks identify digital onboarding as the highest-risk point for synthetic identity exposure. Fraudulent account openings reached 2.1% of financial transactions in 2024, up from 1.27% two years earlier. Synthetic identity fraud accounts for up to 80% of new account fraud.
The ID document is only one part of what is observable at the moment of submission for verification. Before any document is submitted, the session itself may already show signs of elevated risk. Automation tools, virtual machines, location spoofing, and coordinated device infrastructure are all visible at the device layer before any verification check runs. An IDV platform evaluating only the document has no view of the environment in which that document arrived.
Once a user is verified, the platform's signal stops. The same device that cleared onboarding could later be compromised, handed off to a fraud ring, or used to register additional accounts, and the credential layer carries no record of any of it. The document was evaluated. The device behind it was not.
Three moments where device signals change the risk determination
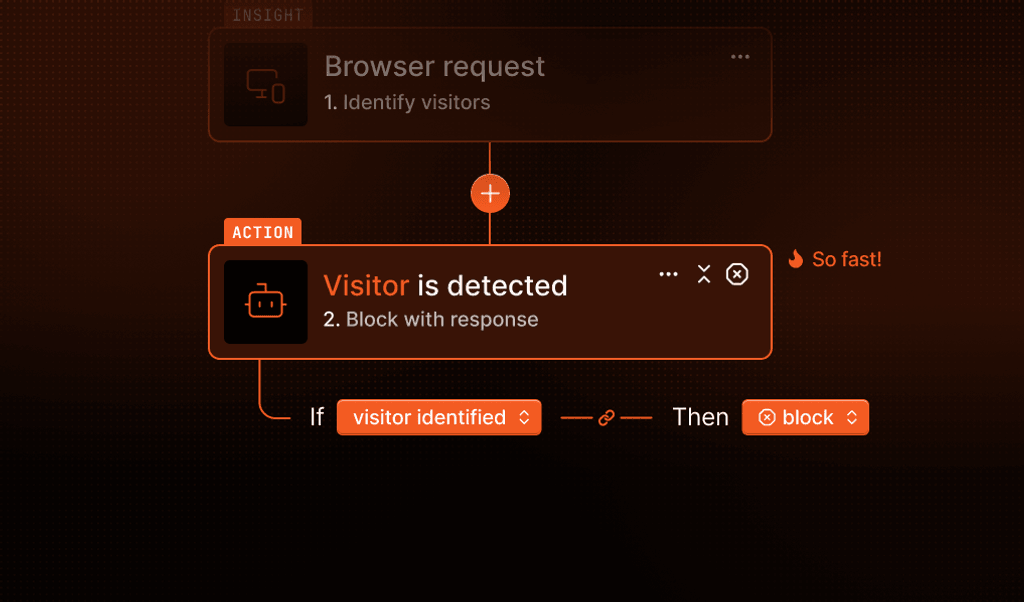
Most identity verification platforms generate meaningful signals at one moment in the verification flow: when the document is submitted. Device intelligence extends that read to the moments before the check begins and the moments after the user has been approved. These are the two points where the current model has no visibility.
1. Before verification
Risk is often visible before any document is submitted. A session arriving from a device flagged for bot activity, a virtual machine, browser tampering, or active location spoofing carries elevated risk before the biometric or document check begins. Smart Signals surface that context at the session level, allowing the platform to apply adaptive friction only when the device environment justifies it. Legitimate users on clean devices move through without interruption. Sessions with elevated risk signals receive additional scrutiny before expensive verification steps are triggered.
2. During verification
A user who submits a high-quality document from a device with no prior history, whose geolocation doesn’t match the declared address, and who is operating through a residential proxy presents a different risk profile than the same document submitted from a known, clean device. The document may be identical. The surrounding context isn’t. Evaluating both together produces a more accurate risk determination than evaluating either in isolation.
3. After verification
Once a user is approved and moves into the customer journey, most IDV platforms stop surfacing meaningful signals. If the same device later appears on a different account, or the account is accessed from a materially changed device environment, the platform has no visibility into the shift. Binding the verified identity to a persistent device identifier at the moment of approval creates continuity for every trust decision that follows. Account recovery, high-value transactions, profile changes, periodic KYC refresh—persistent identifiers empower secure and frictionless processes, without requiring the user to restart the verification process from the beginning.
Building trust for stronger pass rates and conversions
IDV platforms are evaluated on two numbers their buyers care most about: pass rate and conversion. A high pass rate that includes false passes is worse than a lower pass rate with fewer fraudulent approvals. The question platform buyers are increasingly asking isn’t how many users passed, but how many of those approvals held up across the entire customer account lifecycle.
That distinction becomes especially costly at the moments that follow onboarding. During account recovery, high-value transactions, or sensitive account changes, many platforms trigger full re-verification. Each step-up event adds 60 to 90 seconds of friction. Conversion drop-offs can reach 60-70% when onboarding flows become too complex, and 38% of applicants abandon the process when identity verification takes too long. For platforms operating at scale, every unnecessary step-up event compounds quickly into measurable retention and revenue impact.
A persistent device signal changes what those moments require. When a platform can confirm the returning device is the same one that completed the original verification, low-risk actions can proceed without another full verification flow. When device context has changed, or new risk signals have appeared, step-up controls apply to the sessions that warrant them rather than to all returning users equally. The result is fewer unnecessary re-verification events, lower drop-off at friction points, and a pass rate that reflects accurate trust decisions rather than volume throughput.
Identity verification platforms that can offer clients a verified-once, device-anchored trust model are delivering something their buyers can’t get from platforms that apply the same friction universally. That is a product difference, not a positioning one, and it shows up directly in the conversion and retention metrics clients use to evaluate their verification stack.
Four fraud patterns that a document check can’t see
Document and biometric checks establish whether a presented identity is plausible at a point in time. They have no view of what happens across sessions, across accounts, or after the verification event closes. These are the fraud patterns that emerge in those gaps, and the device signals that make them visible.
1. Account farming after verification
Some fraudsters deliberately pass onboarding using real or high-quality synthetic identity material, with no intention of committing fraud at the moment of verification. The account is held and later used for downstream abuse, such as payment fraud, credit exploitation, or resale to other fraud operators. The original verification returns a clean result because, at that moment, it was clean.
The device used during onboarding becomes the anchor. If that same device subsequently appears on other accounts or in fraud-flagged sessions, platforms can surface the connection across the account graph without relying on manual investigation or waiting for the downstream fraud to materialize. Synthetic identity fraud accounts for only 4% of fraud frequency but drives 7% of financial losses, a ratio that reflects the deliberate, patient structure of account farming operations.
2. Credential handoff
A verified account may be sold, shared, or taken over by a different operator after the original verification is complete. The credential may still appear valid, but the device environment has changed. A sharp shift in device data after verification, a different hardware profile, browser configuration, or network pattern, signals that the account changed hands rather than that the original user replaced their phone.
Consider a verified lending account accessed consistently from the same mobile device for three months. After the account sells on a fraud marketplace, a buyer in a different geography logs in from a desktop environment with a new browser fingerprint, a different IP range, and no device history with the platform. The credential is valid. The trust decision, based on the credential alone, looks clean. At the device layer, every signal has changed. Platforms with persistent device identifiers flag the shift immediately. Platforms without them have no basis to distinguish this session from the original user switching phones.
This pattern is not an outlier. Account takeover fraud represents 13% of fraud occurrences and 12% of financial losses. The document check that occurred at onboarding has no bearing on what is happening to the account months later. Device continuity does.
3. Bulk registration using automation
Fraud rings create accounts at volume using headless browsers, scripted tools, or coordinated device infrastructure. Each account may carry a different identity document, but the underlying automation is consistent across attempts. Even failed attempts generate operational cost, review burden, and exposure that absorb platform resources without producing revenue.
What makes bulk registration difficult to catch with document checks alone is that each submission can appear independent. A fraud ring submitting 500 applications across a weekend uses 500 different identity packages (e.g., different names, addresses, and document images), but runs them from the same device infrastructure. The document layer sees 500 separate applicants. The device layer sees 500 sessions originating from the same underlying environment, and can surface that pattern before any document is reviewed.
The scale of automated registration confirms that this is a primary attack vector. Sophisticated fraud nearly tripled to 28% of attempts in 2025, and 8.3% of digital account creations were suspected of being fraudulent in early 2025. Bot Detection at the device layer identifies automated registration campaigns before document submission begins, reducing the volume of fraudulent attempts that would otherwise enter the verification flow.
4. Synthetic identity recycling
A single fraud operation may submit multiple identity documents across repeated registration attempts while reusing the same device or technical environment. Each document may present a different name, address, and identity, but the device remains the same.
The pattern is also accelerating. Synthetic account fraud attempts grew 153% from late 2023 to early 2024, and synthetic identity document fraud surged 311% in North America in Q1 2025. For platforms evaluating each application in isolation at the document layer, those attempts are difficult to connect. At the device layer, the shared infrastructure becomes visible.
The financial exposure reflects how long this goes undetected. U.S. lenders faced $3.3 billion in exposure to synthetic identities tied to new accounts. Estimated U.S. economic losses from synthetic identity fraud now range from $30 billion to $35 billion annually.
How to integrate device intelligence into your verification stack
Document and biometric checks establish who a user claims to be at a point in time. Device intelligence establishes what environment is presenting that claim, whether it has been seen before, and whether the context around it is consistent with a legitimate user. The two layers address different questions, and the practices below show how integrating them changes what identity verification platforms can offer their clients at every stage of the verification flow.
Route sessions by device risk before the verification flow begins
Not every session warrants the same path through the verification flow. Evaluating device context before the document flow starts allows platforms to route higher-risk sessions to stronger controls before committing to expensive verification steps. Sessions that arrive clean move through the standard flow. Sessions that are higher risk can receive appropriate scrutiny before the biometric check runs.
Bind the verified identity to the device at approval
A successful verification decision should carry forward after onboarding. Linking an approved identity to a persistent device identifier creates continuity for every trust decision that follows. Verified users returning on a recognized device can proceed without re-verification. Users returning on an entirely different device environment receive step-up controls proportionate to that change, rather than applied universally to all returning users.
Use persistent device-layer footprints to connect patterns
A persistent device identifier makes shared infrastructure visible across the account graph. Patterns that appear isolated at the document layer, such as separate applicants, separate identities, and separate verification events, often share device-level infrastructure that connects them. Account farming operations, bulk registration campaigns, and synthetic identity recycling all leave device-layer footprints that cross-account analysis can surface before those patterns produce losses.
Extend trust beyond the original verification event
Many of the highest-risk moments occur after onboarding: account recovery, profile changes, payment updates, high-value transactions, and periodic KYC refresh. Keeping device signals active after onboarding allows the platform to make accurate trust decisions as the risk environment around each account changes. Verified users on a recognized device face less friction. Users whose device environment has changed materially face scrutiny proportionate to that change.
Fingerprint: The essential device-layer complement for IDV platforms
Fingerprint was built to solve a very specific problem for web and mobile traffic: Visitor identifiers that degrade or can be evaded. Cookie clearing, incognito sessions, and browser changes cause most device identification approaches to lose continuity, which means the signal that anchors a verified identity erodes over time.
Fingerprint’s visitor identification is engineered to persist through those evasion techniques, producing a stable identifier that remains consistent across the sessions that follow verification, not just the session in which it occurs. Smart Signals extend that further by surfacing bot activity, virtual machine use, VPN use, location anomalies, and browser tampering at the session level before any application-layer check runs.
For IDV platforms, this visitor ID can be a crucial anchor for building trustworthy and reliable verification flows. Without a stable, persistent device identifier, session routing is inconsistent, identity binding degrades after cookie clearing, and link analysis across accounts has no durable signal to work from. IDV platforms can be at risk of blind spots that can impact their pass rates and conversions, and unseen fraudulent activity before, during, and after their verification flows.
For a closer look at how Fingerprint device intelligence can strengthen your identity verification stack, you can start a free trial or contact sales to discuss your specific use case.