As with any online transactions, identity thieves have always targeted government benefits and those who benefit from them. In recent years, however, fraudsters' pandemic payouts have attracted even more interest in taking advantage of new, vulnerable processes.
Fraudsters regularly take advantage of new and vulnerable processes in order to capture compromised funds. A unique opportunity presented itself during 2020 when the US government offered financial benefits (commonly known as a “PPP Loan”) to affected individuals and businesses.
By using compromised credentials, fraudsters were able to file fraudulent claims using stolen identities for false financial gain. A TransUnion report in 2020 said that states may have paid out between $550 million and $650 million in fraudulent claims. Fraudulent claims hurt governments, but they hurt affected businesses and individuals more. Governments will recover, but identity theft can ruin an individual’s credit, stop them from claiming benefits in the future, and cause financial stress for years.
In this article, we’ll explain how identity theft works, how valuable it is to bad actors, how government benefit fraud is affected by identity theft, and what protection measures can be put in place to help prevent identity theft.
Identity Theft Starts with a Single Compromise
Stealing user identities can come in several forms. Still, one common method is when cyber-criminals illegally access and steal personally identifiable information (PII) from a vulnerable business to access a user’s government benefits. Then, cyber-criminals take the stolen data and apply for unemployment benefits, COVID-19 financial assistance, and even tax return refunds from the IRS. Once the government determines benefit payouts are fraudulent, targeted individuals are asked to pay back the money or face jail time.
Cyber-criminals target businesses to steal PII instead of individuals as they represent a much higher upside. A compromise could result in PII theft for thousands of customers and a seven-figure payout for cyber-criminals selling credentials on darknet markets.
The amount of money for each record depends on the data stolen. For example, credit card details and PII linked to the card are worth $150 per record. A business storing 10,000 customer records would be worth $1.5 million for attackers on darknet markets. More lucrative opportunities are worth much more. For example, a hacked Kraken verified account is worth $810 per record, which would bank a crime ring of $8.1 million on darknet markets.
Stolen data is worth big money, so businesses must do everything they can to protect user data. Unfortunately, once it gets out that your business is responsible for identity theft, the negative press will destroy customer trust and loyalty and eventually impact revenue. As a result, businesses risk going bankrupt and losing investors.
Finding the Right Vulnerable Business
So, how do cyber-criminals steal PII from a business? Numerous attacks in the wild give cyber-criminals access to your business environment, but a few stand out in data theft incidents. Credential theft is a primary attack from phishing or social engineering. Phishing is one of the most common vectors for credential theft, and it only takes one employee to fall for it before it becomes a severe data breach. In particular, cyber-criminals are looking to take over an employee’s account by using their credentials to access sensitive information.
Account takeover can be a targeted effort aimed at one employee, or an attacker might send phishing emails to numerous people hoping to trick at least one. The attack is successful if the cyber-criminal can authenticate into the business application as the employee, which means the attacker has the same privileges as the employee’s account.
Alternatively, if attackers have many stolen credentials to test, they can use scripts (often called “bots”) to compromise target accounts automatically. Cyber-criminals may even try login credentials associated with an employee sourced from an entirely different breach, as many people use the same credentials across multiple websites.
Sophisticated attacks make it much more difficult for your organization to detect the compromise. It usually takes months for detection, so the attacker has plenty of time to siphon data using the stolen account and install backdoors leading to additional credential theft. In addition, rootkits installed on an employee’s computer would potentially give an attacker remote control of the machine, adding to the damage.
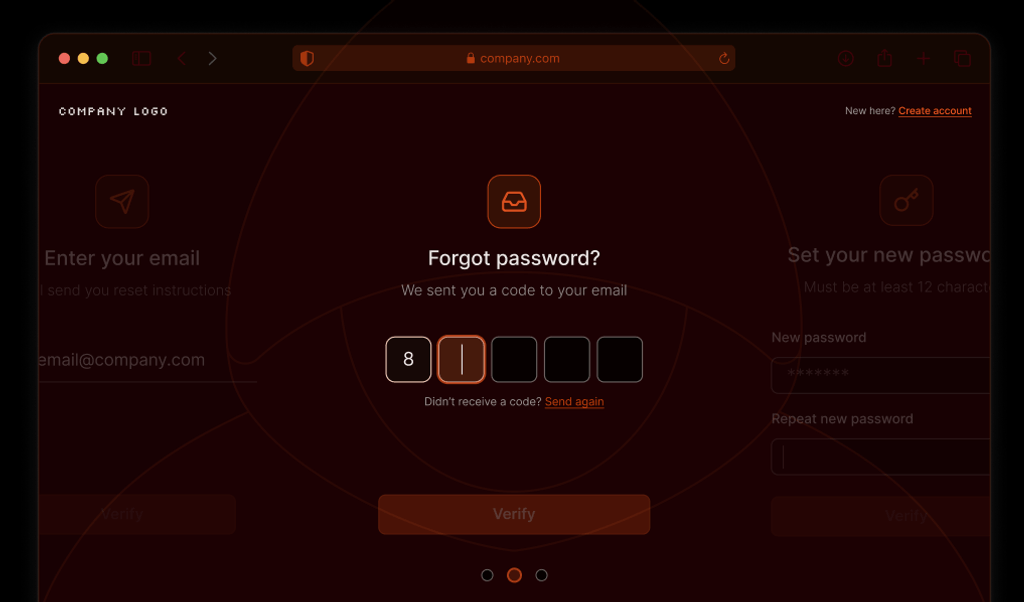
Detecting and Stopping Automated Authentication After Credential Theft
Credential theft severely threatens your corporate data protection, but additional security against account takeovers limits damage. Email security is a good start to stop phishing, but attackers use several tools to trick users into divulging their credentials. Here are some ways to mitigate damages:
- Detect bots on authentication pages. Stop the bots before they have the opportunity to brute force authentication. Identification of a human user versus a bot will mitigate damages on account takeover attempts after credential theft.
- Use multi-factor authentication. Any secondary authentication step mitigates most credential theft. For example, should an employee fall victim to phishing or social engineering, the attacker would still be unable to authenticate into business applications. Couple this with bot detection, and your risk of a data breach is significantly reduced.
- Educate employees on the signs of phishing and its impact on brand reputation. Cybersecurity training should always be a part of onboarding new employees, and it should be a continual effort where employees are educated on the latest threats. In addition, employees should have a point of contact should they think an email or any contact is potentially a threat.
- Monitor your environment continuously. Monitoring is not only good for cybersecurity but it’s required for compliance. You likely fall into at least one compliance regulatory body if you store credit card numbers, PII, healthcare information, or financial data. Good monitoring with artificial intelligence that detects suspicious activity based on heuristics and user behavior patterns can detect fraudulent activity on a hacked employee account. It can detect potential compromise, brute-force attacks, and other web-based threats.
Fraud Will Continue, But You Can Minimize Risk to Protect your Customers from Identity Theft
You can’t completely protect customers from being the target of identity theft, but you can protect your own organization’s environment so that you don’t contribute to the problem. In addition, government benefits are critical for numerous individuals who need assistance, so your customers can suffer financially after a successful data breach.
Fingerprint can help with your cybersecurity and protect web pages from being targets for brute-force attacks. Keep your customers' accounts safe by accurately identifying threats before they cause damage with Fingerprint Pro's highly accurate visitor identification. In addition, should always have a good strategy incorporating several risk-reducing factors. Monitoring, training, multi-factor authentication, and employee cybersecurity awareness benefit your organization’s continuity and success.